This is the second part of blog series about Azure AD Domain Services. In this post I’m going through the implementation of AAD DS. If you would like to read other parts from this series those can be found from:
Azure AD Domain Services aka AAD DS – Part 1
Azure AD Domain Services aka AAD DS – Part 3
If decision is made and organization is ready for enablement phase high level tasks are:
- Configure AAD DS basic settings and create the service
- Configure virtual network
- Create admin group
- Update DNS for virtual network
- Enable password hash sync if hybrid identity model is used
Configure Basics
There are instructions in docs.microsoft.com how to configure necessary settings and I’m not going to cover all the details in here, anyway there are screenshots below from my AAD DS service creation.
Things to keep in mind when planning and deploying Azure AD Domain Services (docs.microsoft.com).
DNS:
- Do not use default DNS name because in certain scenarios it can cause problems, for example enabling LDAPS from Internet. You will not be able to get certificate for onmicrosoft.com domain because it’s owned by Microsoft
Sync:
- Initial synchronization may take from a few hours to a couple of days depending on the number of objects in your Azure AD directory.
- After initial synchronization completes, it takes about 20-30 minutes for changes that are made in Azure AD to be updated in your managed domain. This synchronization interval applies to password changes or changes to attributes made in Azure AD.
Passwords:
- In hybrid environments password hash sync enablement is mandatory.
- If there is a cloud only user who needs to connect to AAD DS their password needs to be changed after Domain Services has been deployed.
Domain:
- Only one managed domain can exists in environment
Network:
- Azure AD Domain Services can be enabled only within single Azure vNet
- vNet Peering can be used to connect other virtual networks to network in which you have enabled AAD DS
Enabling Azure AD Domain Services

Configuration summary

AAD DS deployment automatically creates admin group. Members of this group has permission to manage AAD DS domain and join computers to it. If the group exists duplicate is not created than same group is used like in my environment.

When AAD DS has been created there is an option on the dashboard to configure DNS for virtual network. When configured and applied you can see information (with reboot request) on the top of the dashboard.
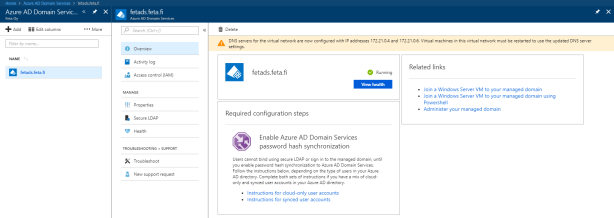
Final task is in Hybrid environments to enable password hash sync. It can easily done via AAD Connect configuration wizard. In my environment I enabled it and run force password sync script to make sure that all password hashed has been synced to the cloud.
How to enable password hash sync in AAD Connect

Joining Member Server to AAD DS
When domain is up and running and all the pre-requisites have been satisfied you can join member servers to AAD DS. Those servers needs to be inside subnet where AAD DS has been associated. Currently you cannot attach AAD DS to multiple subnets but naturally can use vNet peering to routing traffic between vNets.
When joining member server to domain use account which is member of the AAD DC Administrators group, in my case I’m using ds-admin account. When joined to domain connection works with users who is member of the AAD DC Administrators group.

Summary
AAD DS deployment has been made relatively easy. Hopefully this will give better understanding and helps you with deployment.
