Last week I wrote how to identify Azure security alerts with different tools available in cloud. At 28th February Microsoft published cloud based SIEM tool named “Azure Sentinel”. I heard rumors about this product back in autumn 2018 and have been eagerly waiting it since.
What is Azure Sentinel?
A cloud based SIEM by Microsoft which has been built a top of Azure Log Analytics. Next section contains product description from docs.microsoft.com:
Microsoft Azure Sentinel is a scalable, cloud-native, security information event management (SIEM) and security orchestration automated response (SOAR) solution. Azure Sentinel delivers intelligent security analytics and threat intelligence across the enterprise, providing a single solution for alert detection, threat visibility, proactive hunting, and threat response.
Azure Sentinel is your birds-eye view across the enterprise alleviating the stress of increasingly sophisticated attacks, increasing volumes of alerts, and long resolution timeframes.
- Collect data at cloud scale across all users, devices, applications, and infrastructure, both on-premises and in multiple clouds.
- Detect previously undetected threats, and minimize false positives using Microsoft’s analytics and unparalleled threat intelligence.
- Investigate threats with artificial intelligence, and hunt for suspicious activities at scale, tapping into years of cyber security work at Microsoft.
- Respond to incidents rapidly with built-in orchestration and automation of common tasks.
First Look
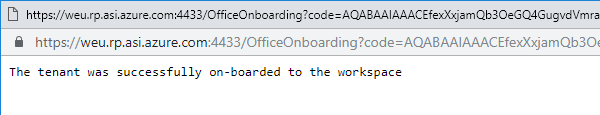
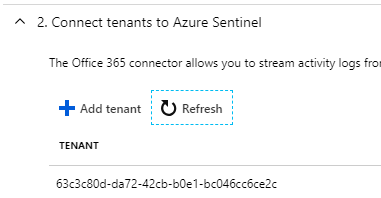
Sentinel is currently in public preview and free of charge (without SLA), definitely worth of testing. Onboarding is very easy, in practical you need to connect Sentinel to Log Analytics Workspace and then you are ready to go.
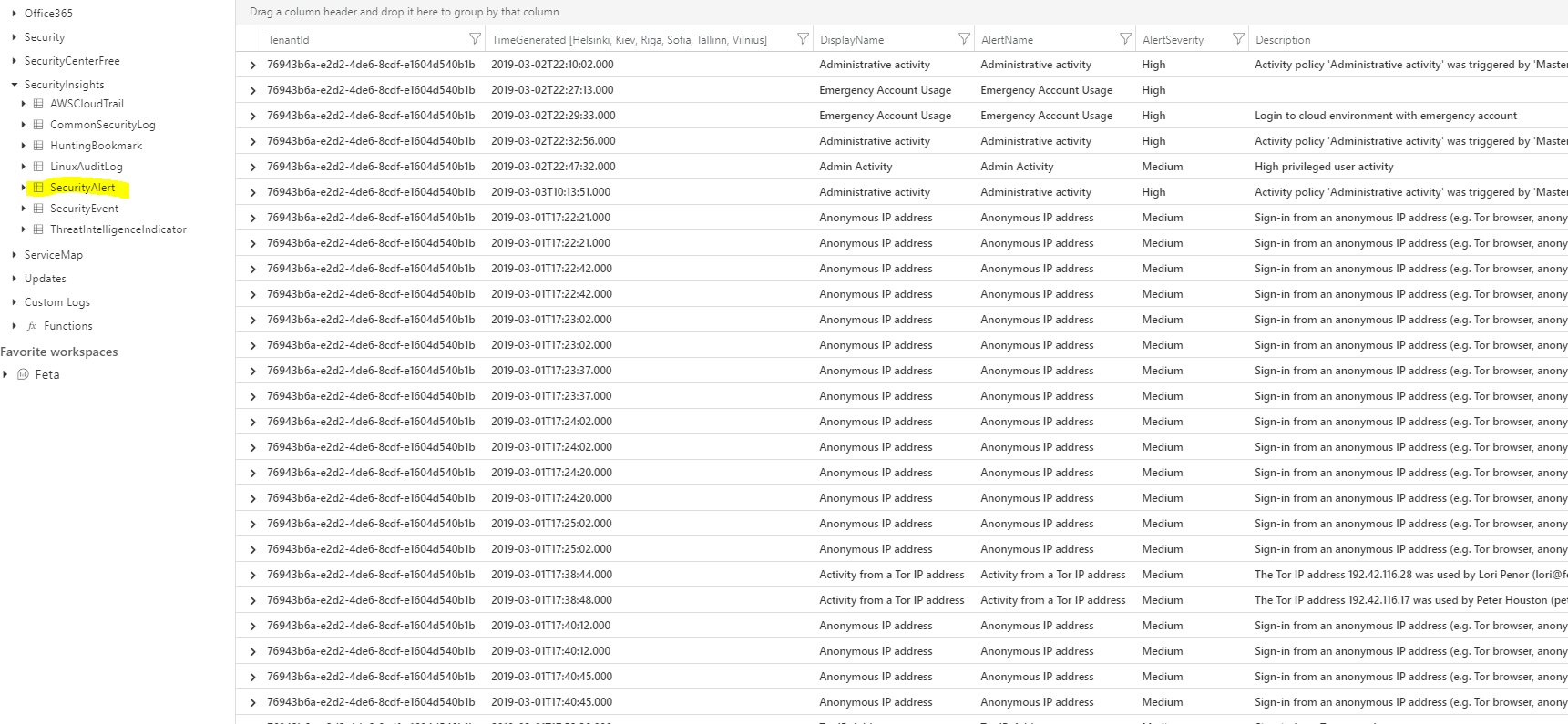
When onboarded, the “SecurityInsights” is added to Log Analytics schema which contains security alerts, hunting bookmarks and so on.

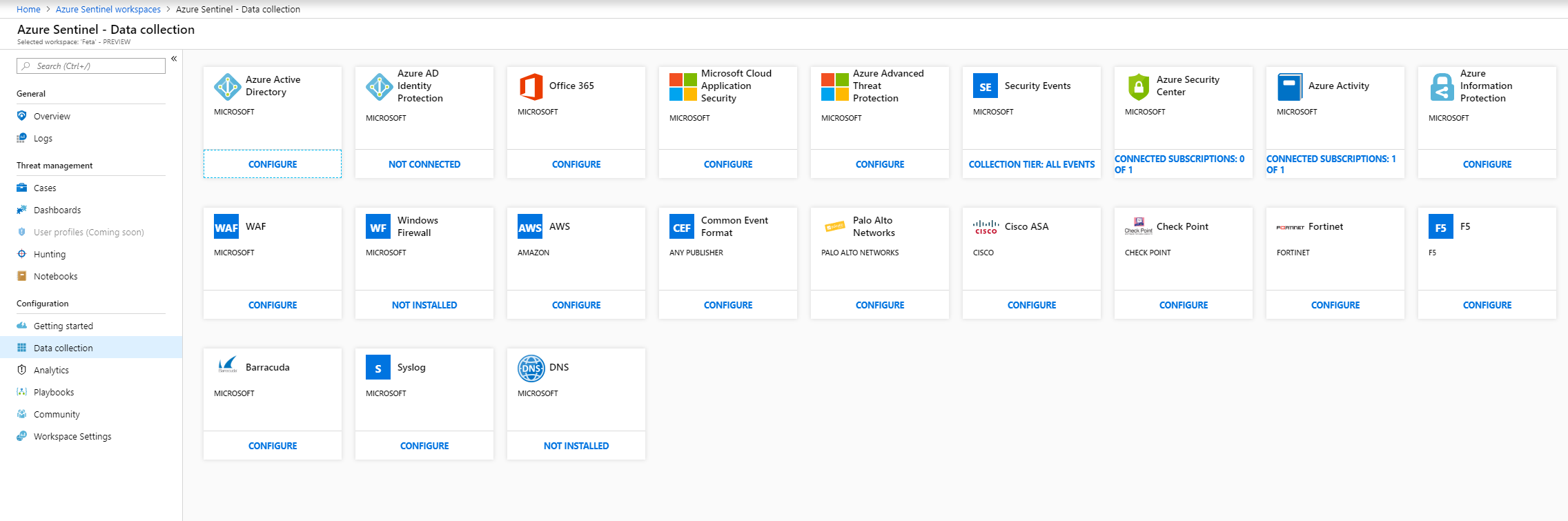
After onboarding it’s time to configure data sources to Sentinel and as you can see there is quite many built-in connectors in place. I configured following ones to my environment:
- Azure AD
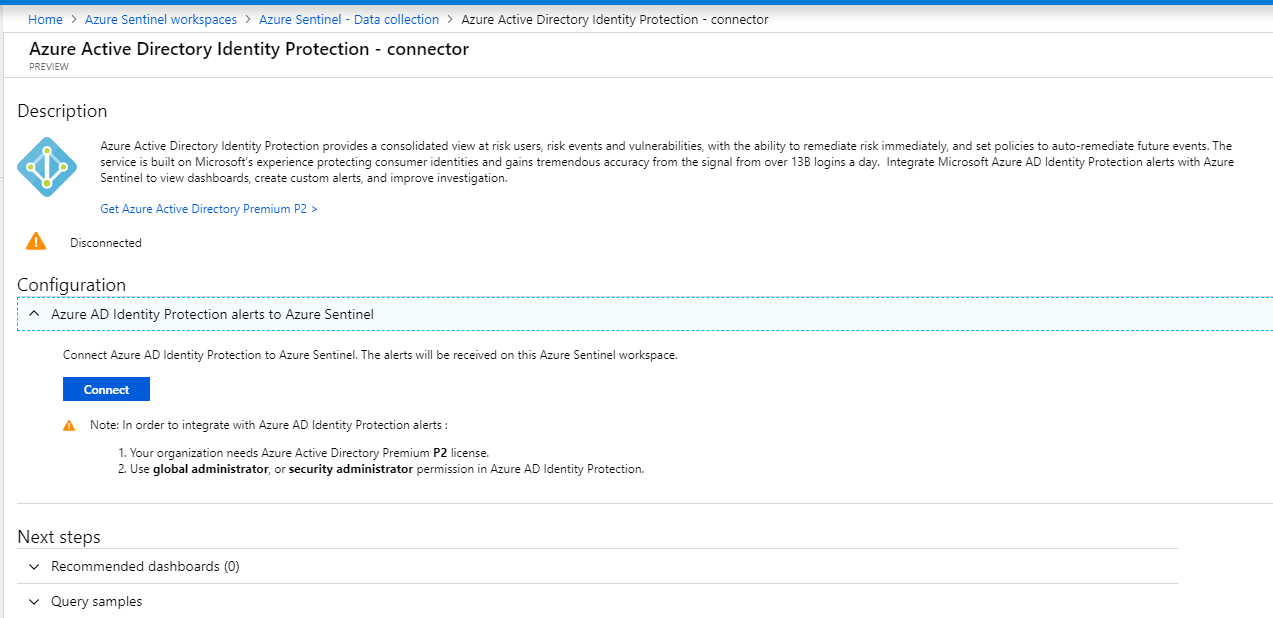
- Azure AD Identity Protection
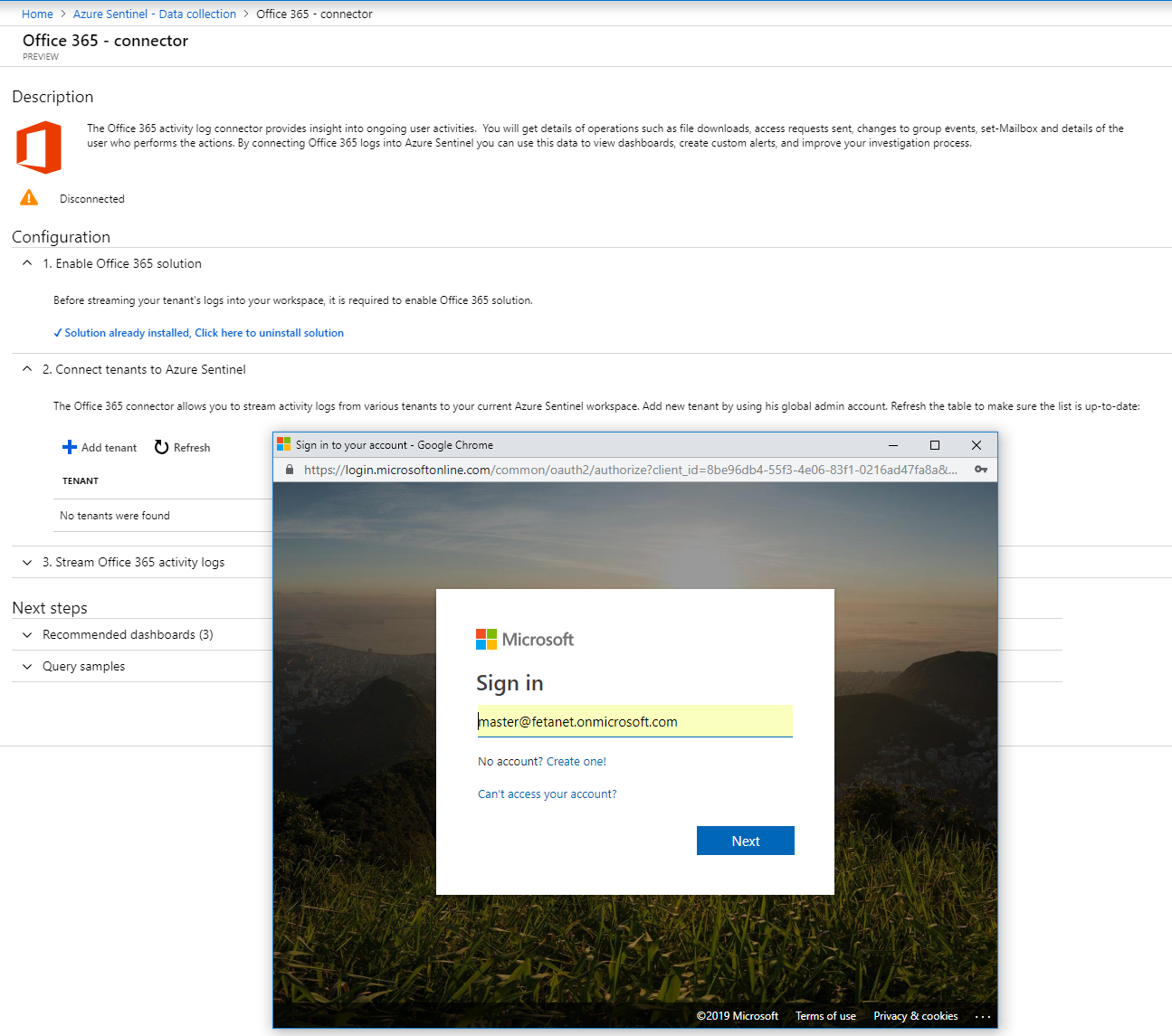
- Office 365
- Microsoft Cloud App Security
- Security Events
- Azure Security Center
- Azure Activity which means subscriptions
- Azure Information Protection
To configure connector just press connect and enter your credentials (Global Admins or Security Admin) when needed. When connectors has been configured navigate to dashboards blade (last picture) where you can see the created dashboards for solutions.

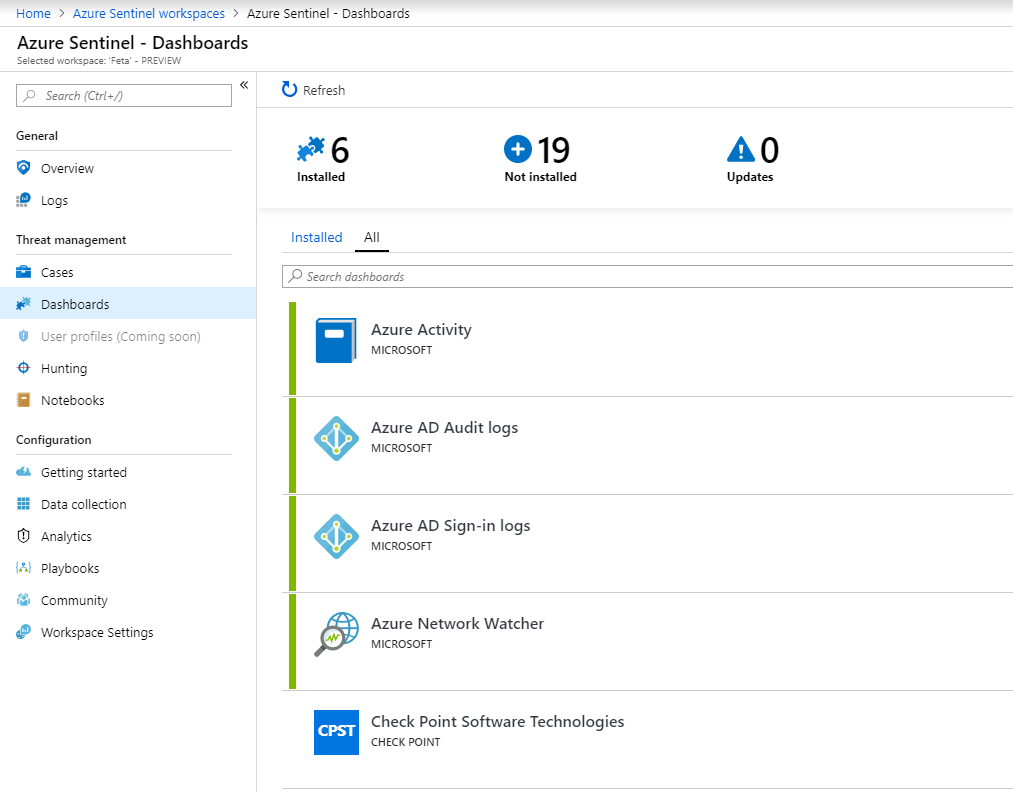
When dashboard is created it can be found from Azure dashboard blade. Note that in preview mode all the connected solutions doesn’t have dashboard available. Worth to look the community resources.

Analytics
This is the place where fun begins. From analytics blade you can create Alert rules based on data which has been collected from data sources.
In my environment I created three rules:
- Sign-in from Tor networks – (event recognize in multiple sources but first provider Azure AD Identity Provider aka IPC)
- Emergency account usage – custom alert based on Azure AD sign-in activity
- High Privileged Account usage – alert triggered by MCAS




Cases
Cases are created automatically based on collected data and alert rules created earlier. From here events can be further identified and investigated including assigning owner and status information.
All security alerts are found from Log Analytics which is connected to Azure Sentinel
Summary
How cool is this, cloud based SIEM product by Microsoft:) It’s extremely interesting to see how Sentinel will position in to market in coming years. At first look, Azure Sentinel looks very promising.