Here is a quick guide how to publish and configure AD FS Service via Windows Application Proxy (WAP, which is former AD FS proxy). I assume that you have your AD FS farm instance up and running.
Pre-requirements
1. AD FS instance installed and configured
2. WAP server W2012 R2 OS installed and server at workgroup
3. certificate (in my case sts.monae.info) copied to WAP server
4. name resolution working from WAP to AD FS instance. I used host-file to confirm name resolution functionality
When installing WAP server launch Server Manager and select Add roles and features
Press next until you can select “Web Application Proxy”. Select also needed features to be installed

When installation of WAP has been finished rest of the configurations will be done with configuration wizard. Select publish from the right corner

Configure Pass-Through authentication
“Web Application Proxy also allows pass-through preauthentication, which enables you to publish applications that do not require preauthentication or whose clients do not support the available authentication capabilities”.
When you publish applications through Web Application Proxy, the process by which users and devices are authenticated before they gain access to applications is known as preauthentication. Web Application Proxy supports two forms of preauthentication:
• AD FS preauthentication—When using AD FS for preauthentication, the user is required to authenticate to the AD FS server before Web Application Proxy redirects the user to the published web application. This ensures that all traffic to your published web applications is authenticated.
• Pass-through preauthentication—Users are not required to enter credentials before they connect to published web applications.
Pass-through preauthentication has no impact on whether an application requires users to provide credentials to the application. That is, an application configured with pass-through preauthentication does not require users to enter credentials to get into the corporate network, but may require users to enter credentials to view the application content.
Configure AD FS instance details. URLs needs to be same and reachable from internet and from internal Network.

Configuration is ready and your AD FS has been published via Web Application Proxy

Workplace Join functionality
Requirements:
1. sts.monae.info A record in DNS (contains IP address of the AD FS server. This is needed during AD FS farm installation)
2. enterpriseregistration Alias (CNAME) which points to sts.monae.info
3. AD FS instance needs certificate which contains following details (examples from my test lab)
a. Common name – sts.monae.info
b. SAN – sts.monae.info
c. enterpriseregistration.monae.info
4. Configure AD FS to allow Device Registration
5. Windows 8.1 client at workgroup
6. Domain user account which has permission to application
7. Application which supports claims. I configured my own application with this guidance http://technet.microsoft.com/fi-fi/library/dn280939.aspx
Perform following commands with PowerShell at AD FS server
Initialize-ADDeviceRegistration (with AD FS Service account). My account is normal user account named svc__adfs, not gMSA

Get-AdfsDeviceRegistration & Get-AdfsDeviceRegistrationUpnSuffix – you can see that there are no SSL port and bindings set

Set-AdfsSslCertificate -Thumbprint thumbprint (Thumbprint is tb from sts.monae.info SSL certificate)

Get-AdfsDeviceRegistrationUPNSuffix – Now SSL settings are in place

if Proxy is in use perform following command at Proxy servers
Update-WebApplicationProxyDeviceRegistration
Default inactivation setting (before Computers are removed from Service) is 90 days. I set it to 20 days in my test environment
Set-AdfsDeviceRegistration -MaximumInactiveDays days

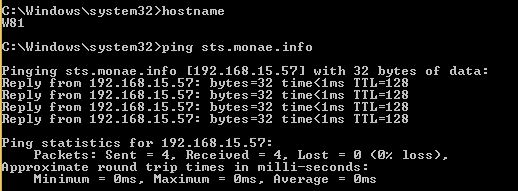
It’s time to add workgroup Computer to workplace. Name resolution is working as expected
Computer is now joined to workplace

My test user doesn’t have to authenticate separately with form based authentication to ADFS (application might still require credentials). Reason for this is that I configured AD FS Proxy with “pass-through Pre-authentication” and in that circumstances user credentials are not required. “Device Authentication” is also enabled in AD FS Service and Computer can be identified and joined to Workplace with this new and cool feature.

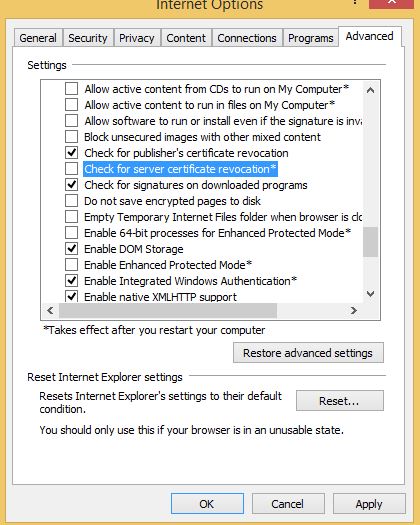
There were couple of issues that I want to bring forward. First one was certificate revocation checking. I was not able to join my laptop to workplace before I disabled revocation checking feature from IE (I was getting event Id 102 to Workplace Join log).
This can be done from advanced IE settings
Second one was device authentication error after Computer was joined to workplace. It caused the login through the federation servers to fail, and the event id 364 was logged on the ADFS servers. At the end of the event logs “Exception Details” first line it said: MSIS5000: Authentication of the device certificate failed.
Extended Protection needs to be disabled on the ADFS Servers because it is unsupported with Integrated Authentication.
Disabling Extended Protection is done by running this powershell command on the primary ADFS Server:
Set-adfsproperties -extentendedProtectionTokenCheck None

After command you have to restart all AD FS server of the farm









Hi
With Workplace Join I understand for Windows 7 devices they must be domain joined to enrol using a Microsoft package to do that. That’s fine.
Lets say that Windows 7 device is a corporate laptop and is now workplace joined by doing this at work.
If I then take that laptop home will ADFS require I am still on the corporate LAN to think I am workplace joined or will that laptop behave like a Windows 8.1 device?
Could I stay off the corporate lan for the device registration maxinactivitytimeout value (90 days) without having to enrol again?
Tony
Hi Tony,
When WP Join came out it was only supported by windows 8.1 + iOS OS and I haven’t tested it with W7. More information can be found from here:
http://blogs.technet.com/b/adhall/archive/2014/03/11/workplace-join-for-windows-7.aspx
https://technet.microsoft.com/en-us/library/dn609827.aspx
https://technet.microsoft.com/en-us/library/dn554247.aspx -> Check WP Join requirements
I’m not sure but I assume that behavior is same than a W8.1 machine. I’ll post an update when I have tested WP join with Windows 7. If you have more information about it please let me know.
Thanks,
Sami