Microsoft Defender for Cloud Apps (MDA) provides visibility for files and related activities from connected applications. With MDA & application integrations you can achieve the following files related scenarios:
- Monitor file activities
- Generate data management reports
- Governance actions for files based on MDA policies
- Azure Information Protection integration – labeling & protecting of data
In this blog, I will shed the light on how MDA detects malware from the connected application and how you can automatically set governance actions for the detected file with file policies.
Disclaimer: Even though I’ve demonstrated all scenarios (malware detection & governance actions quarantine & trash) found in this blog in my own demo environment the scenarios were verified in the production environment. In both environments, the latency and behavior were identical.
In the demo environment, all detections were made with test eicar files from different sources and naturally in the production environment malware files were true positive findings. Different malware types were not tested and the focus of this research was purely on Defender for Cloud Apps policies and file governance actions.
Prerequisites
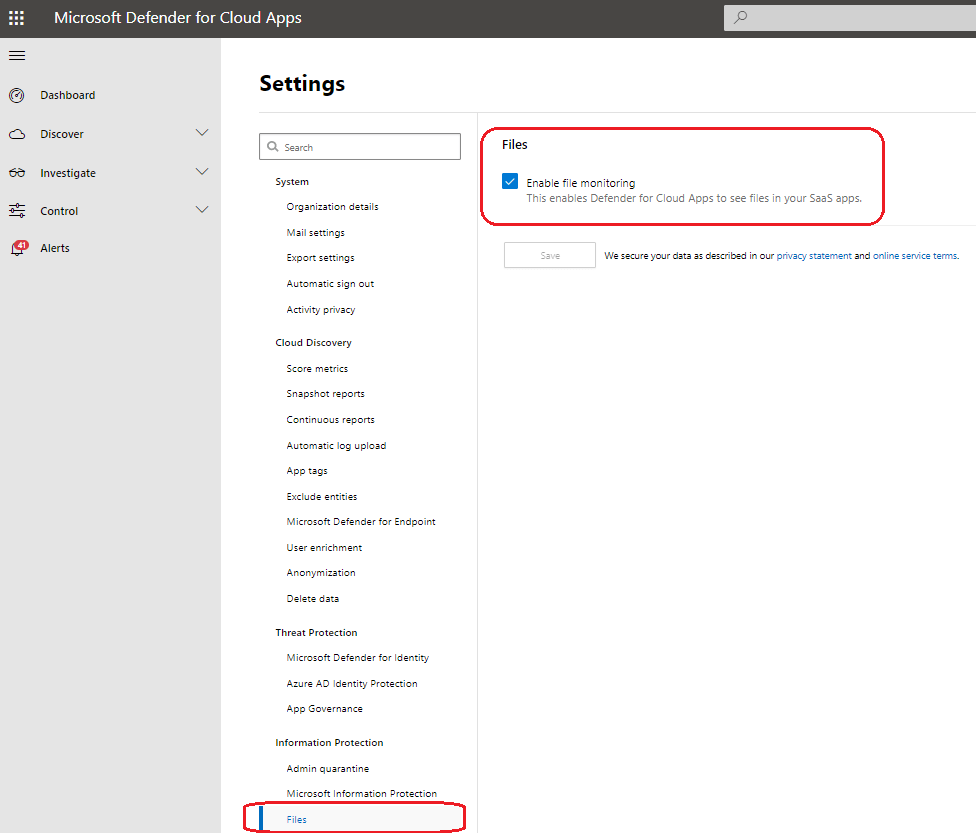
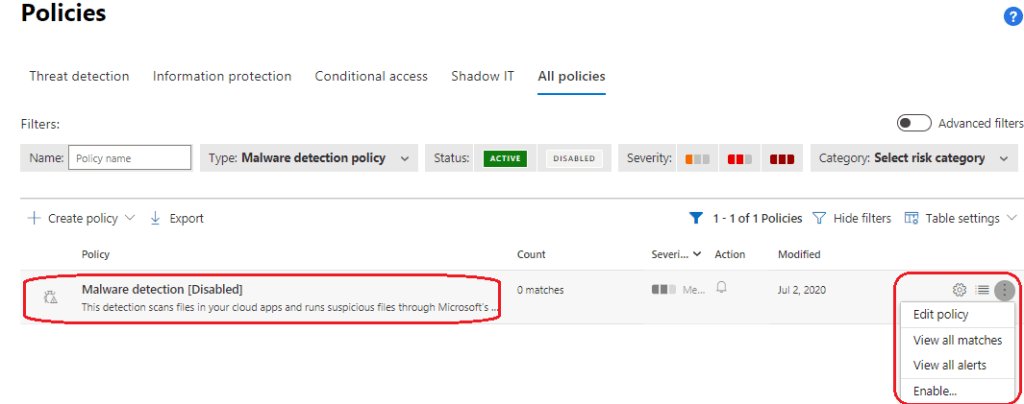
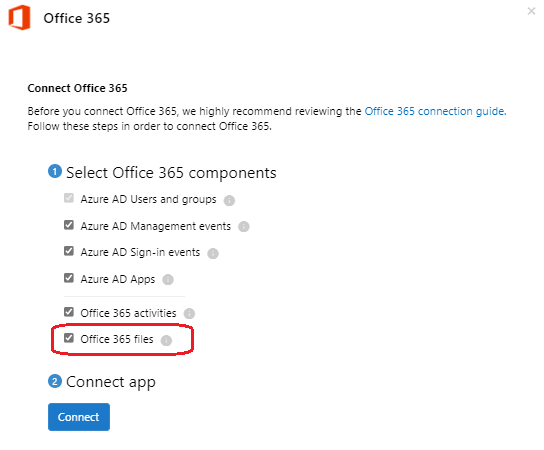
To leverage the file monitoring it needs to be enabled in MDA settings. Besides enabling file monitoring, a built-in malware detection policy is disabled by default & file scanning is not enabled in the O365 data connector (these need to be enabled manually).
- Enable file scanning
- Enable ‘Malware detection’ policy
- Enable file scanning in the O365 data connector
File Policies
MDA offers a wide range of built-in policies for different scenarios and a possibility to create custom policies based on organization needs. From the pictures below you can find active policies on the left and policy templates on the right (malware policy is in its own category).
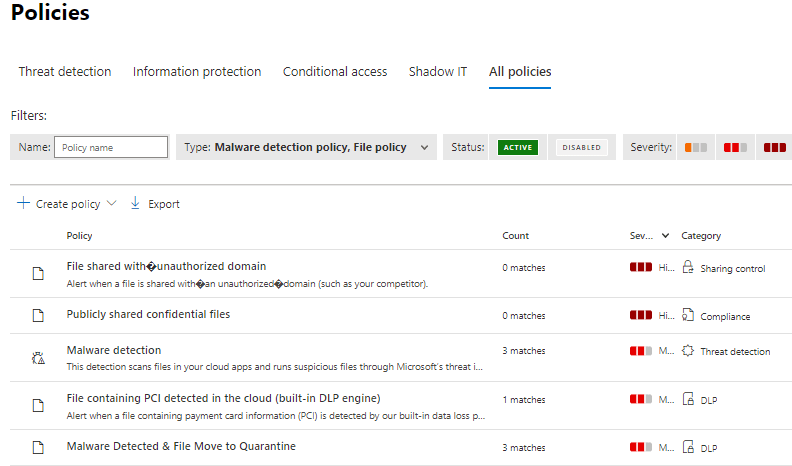

Malware Policy
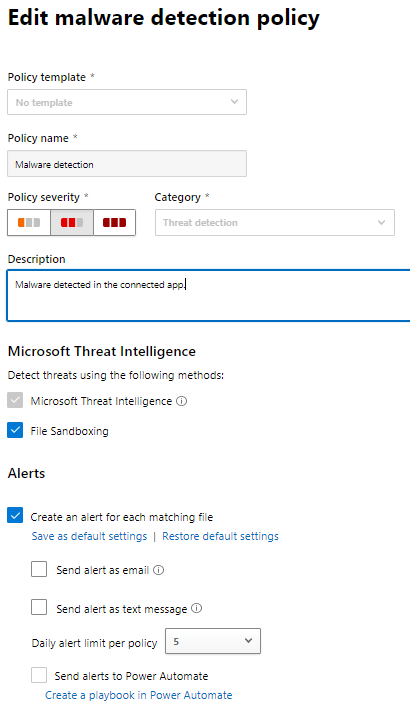
The policy description states: “Detect files containing malware in your cloud environments by utilizing the Defender for Cloud Apps integration with Microsoft’s Threat Intelligence engine. This detection is automatically configured out-of-the-box to alert you when there is a file that may contain malware”.
Currently, the detection is supported in Office 365, Box, Dropbox & Google Workspace. It’s important to understand that when malware is detected in O365 the file is automatically blocked by the app (in minutes since the file is uploaded) and the user is not able to open the file (only the app’s admin has access).
In Box, Dropbox, and Google Workspace, Defender for Cloud Apps doesn’t block the file, but blocking may be performed according to the app’s capabilities and the app’s configuration set by the customer.
The nice thing about the file handling with MDA is that you don’t see file context and operations are run by the backend without an admin user context.
Side note: My experience is that it’s quite an uncommon situation that MDA detects a huge number of malware from files. In most environments I work with, the Microsoft security solution (XDR stack) is deployed, or 3rd party solutions and the first barriers to detecting & protect from the potential malware are solutions that protect collaboration workloads and endpoints. In MS stack these are Defender for O365 (MDO) & Defender for Endpoint (MDE). If both of the aforementioned solutions (MDO & MDE) have been deployed you are not seeing many alerts in MDA.
That being said, I’ve seen situations where MDO is not fully deployed and MDA detects hundreds of potential malware files from the environment. So, it really depends on the environment configuration.
Governance Actions
I often see that MDA is used for activity monitoring without any governance actions. The solution provides governance actions for ‘Activity’ & ‘File’ policies. Available actions depend on the source application. For example, O365 (ODfB & SPO) has different actions available than Dropbox & Box applications.
File Governance actions (more from docs)
- Notifications
- Governance actions in apps
- Labeling
- Change sharing
- Quarantine
- Trash
Activity Governance actions (more from docs)
- Notifications
- Alerts
- User email notification
- Notify additional users
- Governance actions in apps
- Suspend user
- Require user to sign in again
- Confirm user compromised
Use Case – Quarantine Malware Infected Files
In the case I’ve been working with the wanted outcome was to MDA automatically handle detected malware-infected files. The idea was that SOC analysts don’t need to manually remove the file when needed. This scenario works with the newly detected files because after initial scanning MDA scans only new and modified files. For the older files, there is a trick, see the configuration.
Configuration
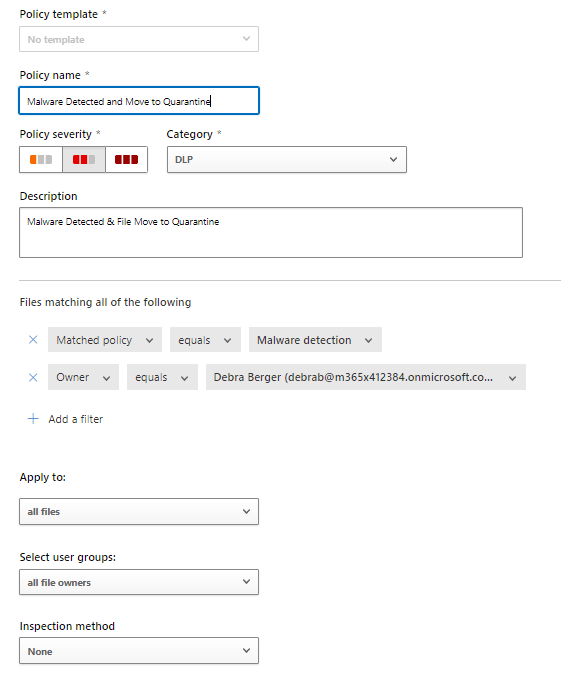
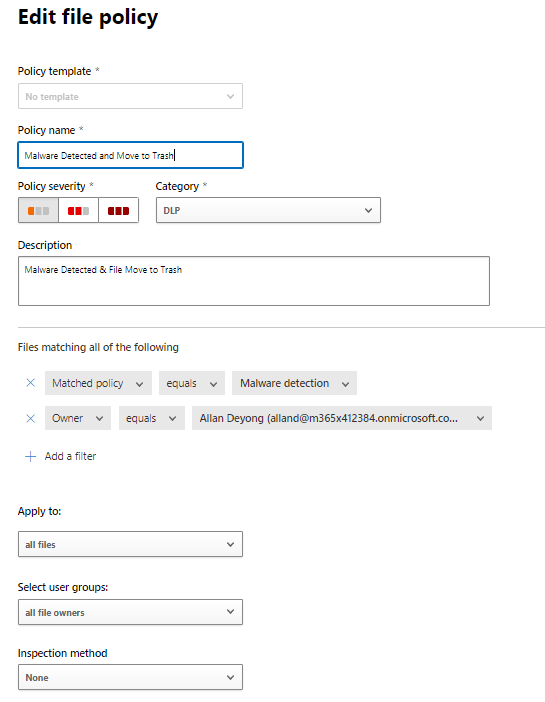
To accomplish the aforementioned scenario you need to configure a custom policy that does governance action when the malware detection policy detects potential malware. This policy can be configured and filtered based on your needs. I always test policies by scoping them to pilot groups to avoid an unwanted outcome.
Note: Be extra careful when configuring file policies with governance actions to avoid data loss from end-users.
The policy below contains the following key values:
- File filtering: matched policy equals malware detection policy
- Scoping: File owners have been defined
- Apply to: All files
- Alert: Create an alert for each detection to monitor the situation
- Governance action: Send policy-match digest to file owner
- Governance action: Put in user quarantine

User Experience
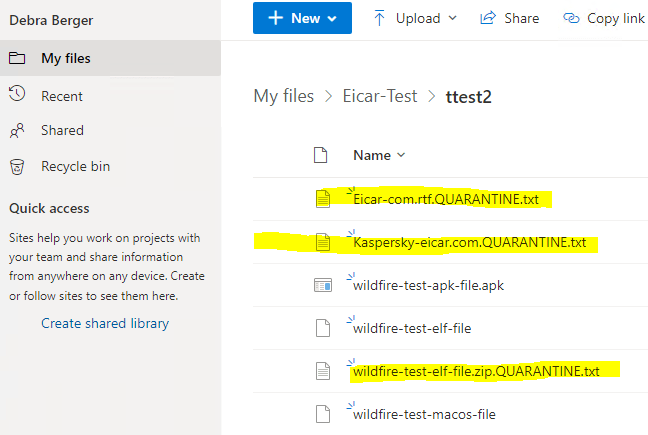
When policy is run and it detects malware & performs governance actions the following actions will take place (OneDrive as an example):
- Alert is created on MDA
- The file is removed from the ODfB folder to a folder named ‘Quarantine’
- Action is made by the SharePoint app
- The original file is deleted and the tombstone file is uploaded to the original location (3rd picture)
When you restore the file:
- Original shares are not restored, default folder inheritance applied
- The restored file contains only the most recent version
- The quarantine folder site access management is the customer’s responsibility

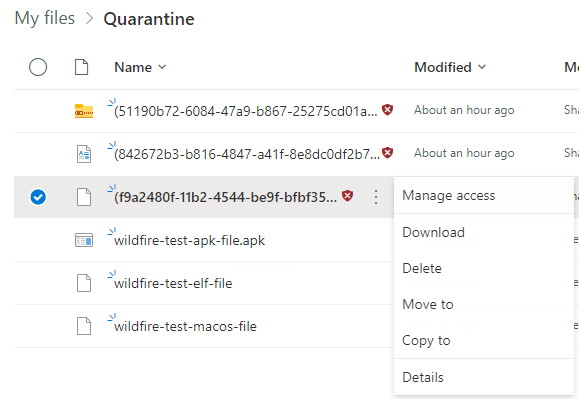
When the file is in quarantine naturally actions are limited
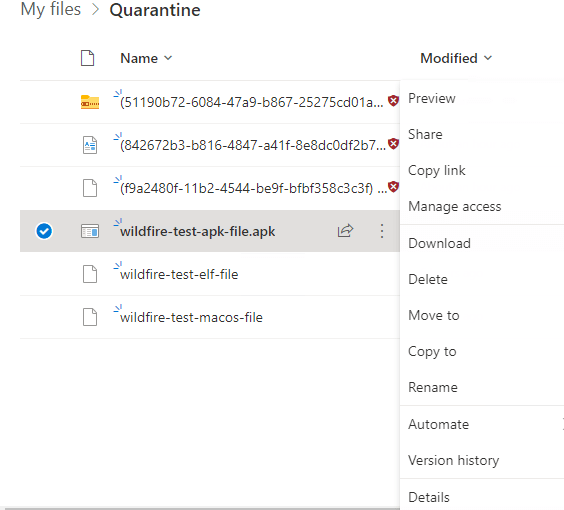
- On the left picture – file in quarantine
- On the right picture – file not in quarantine
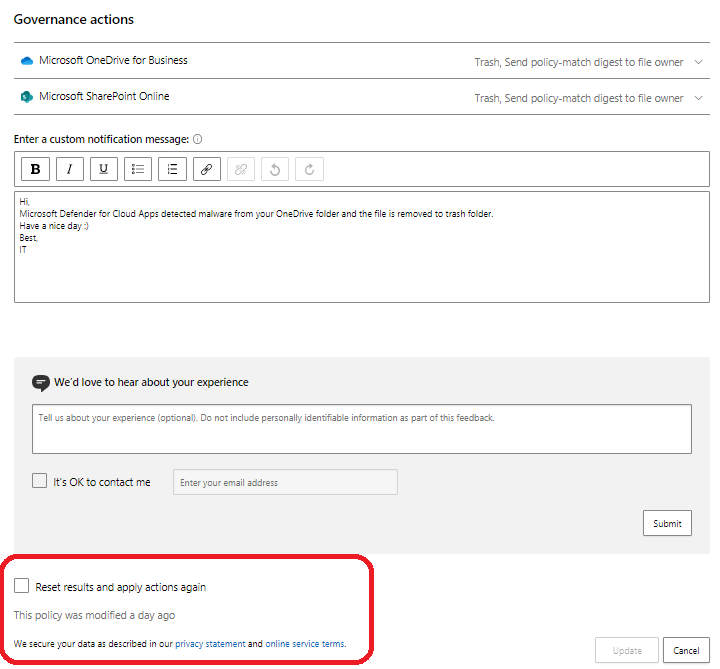
How to process older files
Bottom of the policy configuration you can find the check box “Reset results and apply actions again”. By checking this and saving the policy you can trigger the policy to run governance actions again for all detected files. By triggering this we’ve been able to clean malware detected files by MDA from the O365 workloads and move those ones to the quarantine/trash folder.
Available Actions for Quarantined File
The following actions are available for a file that is moved to quarantine folder:
- Revert the file by the admin
- Release from user quarantine
Use Case – Move malware-infected files to Trash
Another use case is to use governance action that moves potential malware files to the user’s trash folder when it’s detected. When a file is moved to the trash it’s more straightforward to restore the file to use when needed and we can be sure that the files are permanently deleted from the end-users folders at some point in time.
Configuration
MDA policy is identical compared to quarantine policy except governance action is different (Trash instead of user quarantine).
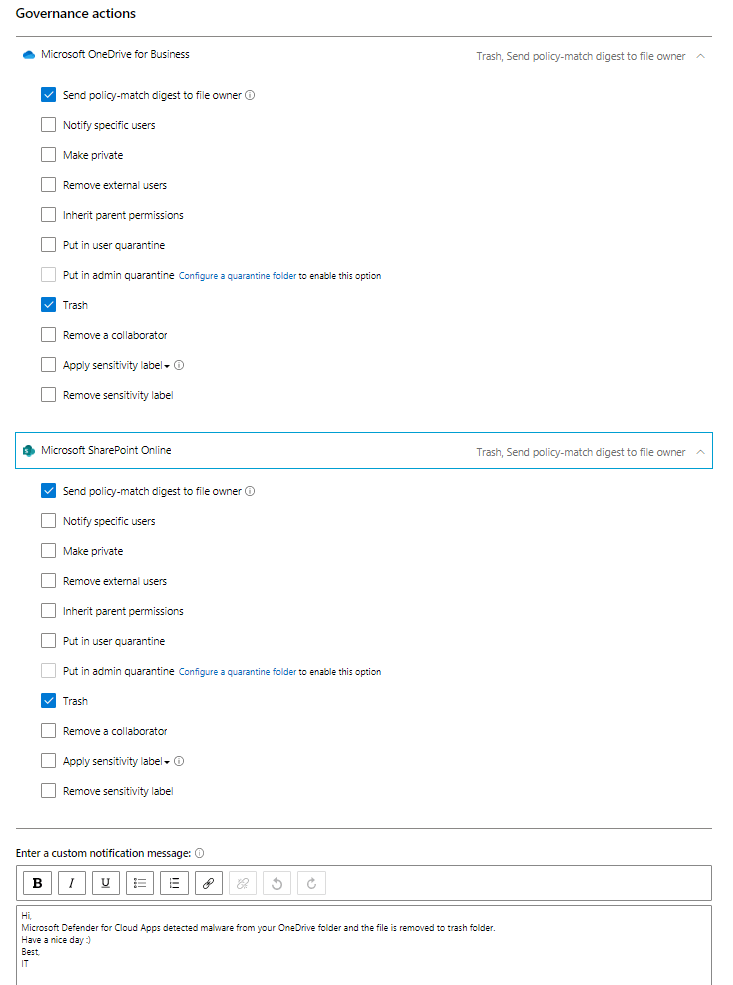
User Experience
When malware is detected by built-in policy an additional custom policy is run with the governance actions. The file is removed from the initial folder to the trash folder as you can see from the pictures below.
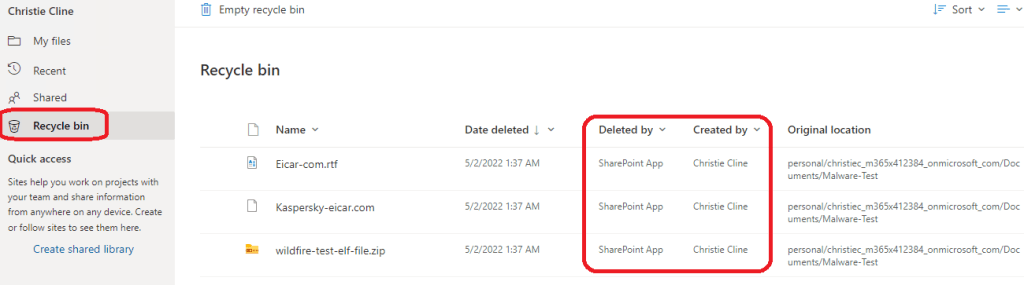
Available Actions for Trashed File
The following actions are available to a file that is in the trash folder:
- Permanent delete
- Restore
MDA Alerts
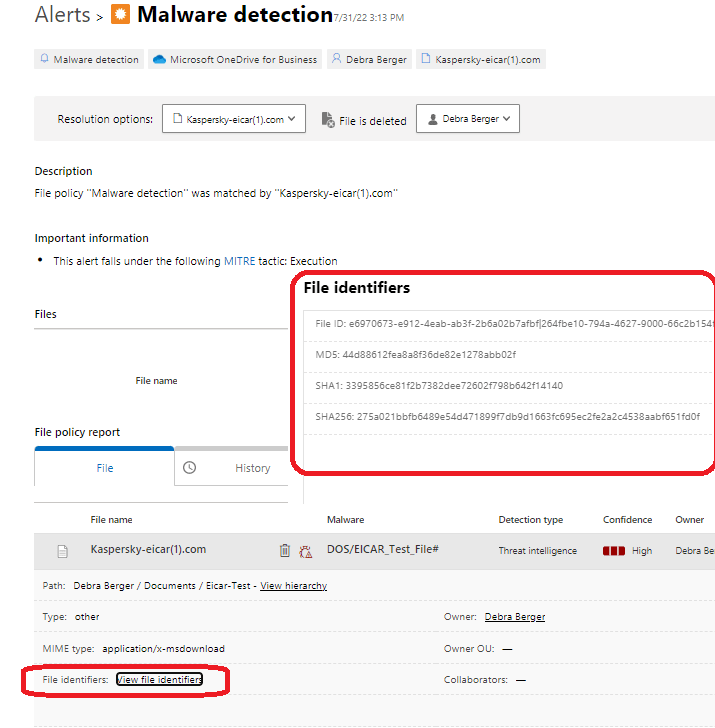
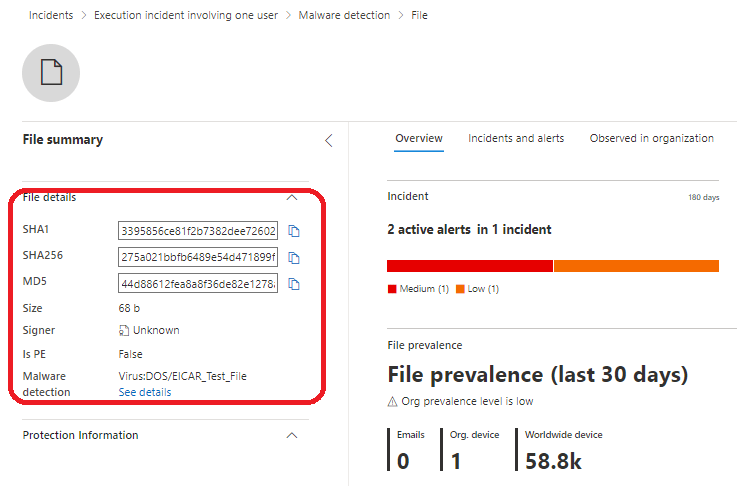
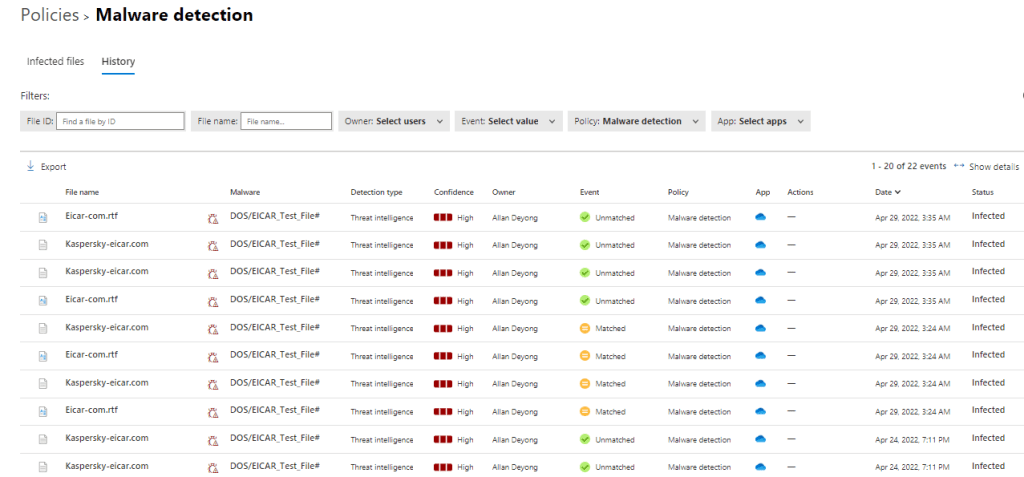
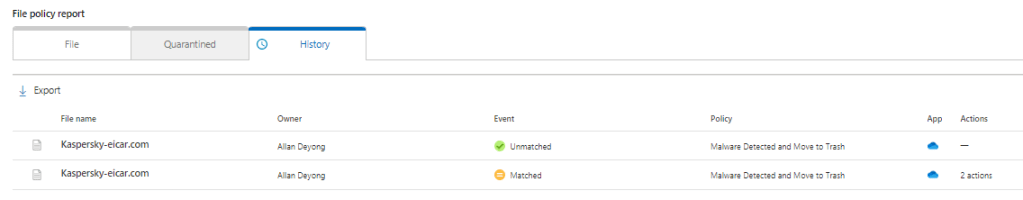
When malware is detected by a built-in policy an alert is created to the alert queue and detailed information is found on the alert page. From the history sheet, you can find possible governance activities made to the file which is very beneficial information. The governance actions are also found in the governance log (located underneath settings).
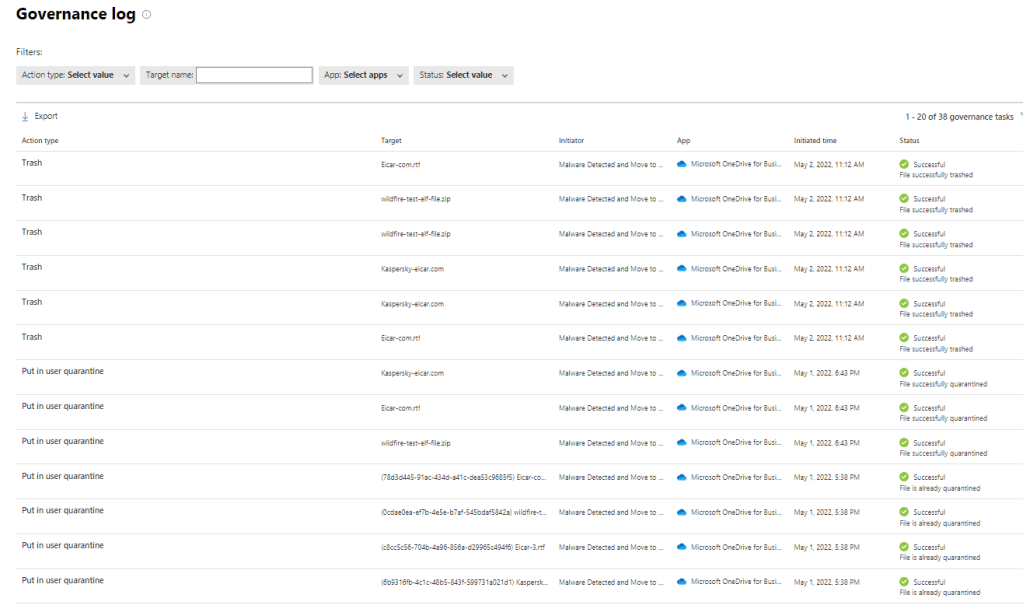
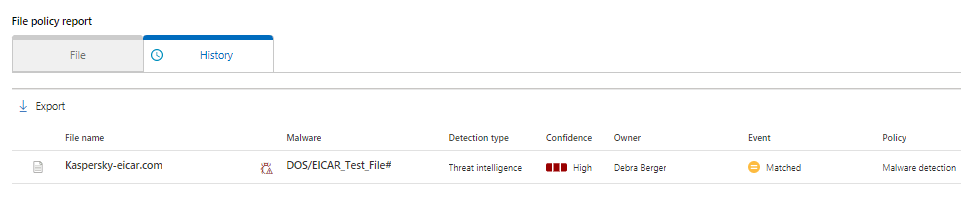
Malware Detection
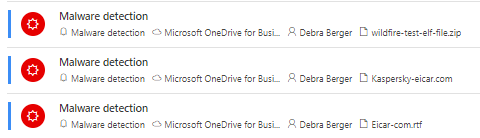
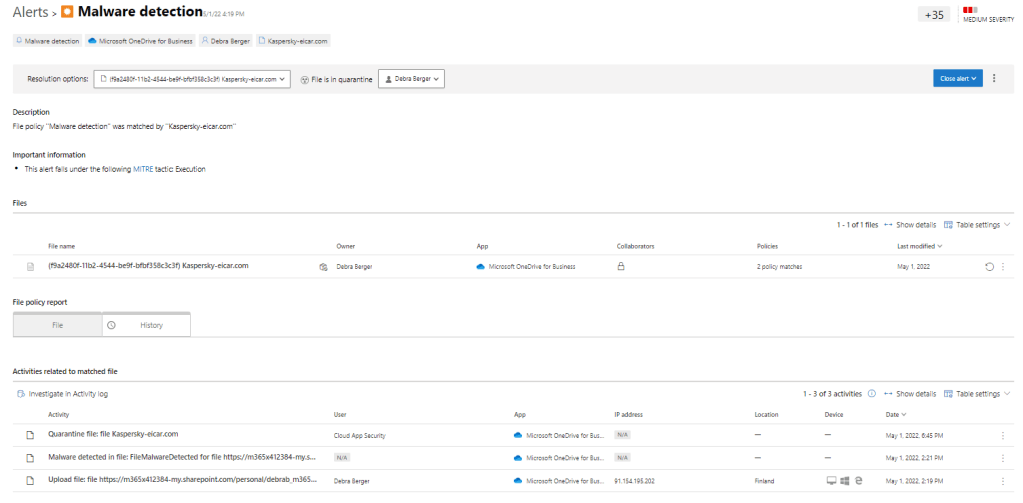
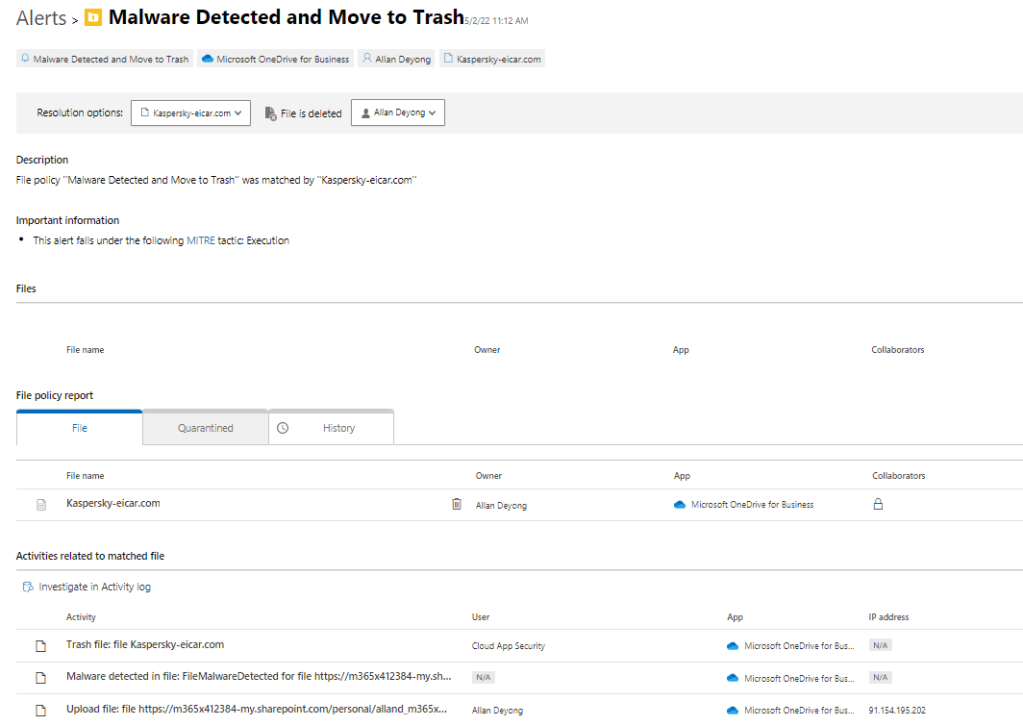
Malware Detection & File Moved to Trash

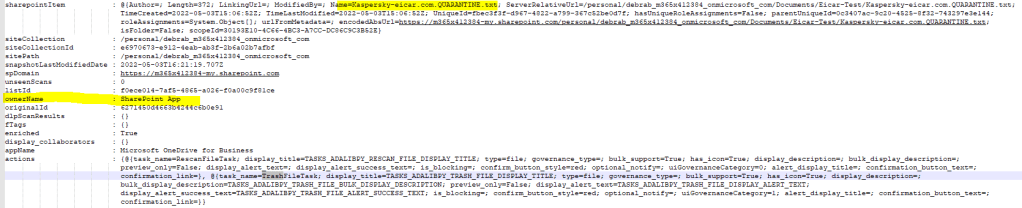
Activity Types from raw data
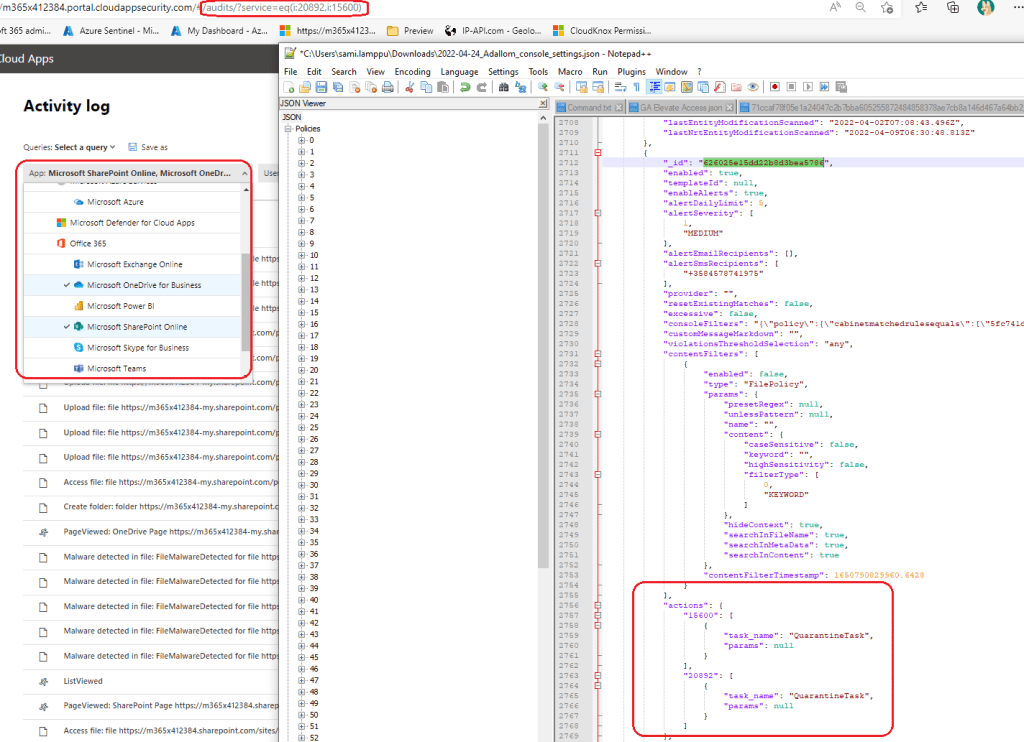
Even though, I’m not a fan of the ‘Defender for Cloud Apps’ API it offers even more detailed information about the files as you can see below. Because governance actions are made the file is owned by the ‘SharePoint’ app.
Simple KQL query to run in M365 Defender to find out all ‘quarantine’ or ‘trash’ activities performed to files.
CloudAppEvents
| where Timestamp between (ago(3d) .. now())
| where ActionType == 'quarantineFile' or ActionType == 'trashFile'
| where ObjectType == 'File'
| project Timestamp, AccountDisplayName, ActionType, Application, ApplicationId, ObjectName, ObjectIdMDA Activity Log filter (paste to the browser by replacing your own tenant name in m365x412384)
https://m365x412384.portal.cloudappsecurity.com/#/audits/?activity.eventType=eq(15600:EVENT_O365_TASK_QUARANTINE_FILE:quarantineFile,20892:EVENT_O365_TASK_QUARANTINE_FILE:quarantineFile,15600:EVENT_O365_TASK_TRASH_FILE:trashFile,20892:EVENT_O365_TASK_TRASH_FILE:trashFile,15600:EVENT_O365_ONEDRIVE_FILE_MALWARE_DETECTED:FileMalwareDetected,20892:EVENT_O365_SP_FILE_MALWARE_DETECTED:FileMalwareDetected)Caveats
When performing governance actions on files from connected applications you need to extra pay attention to policy configuration to avoid unwanted data loss. That being said, use the ‘preview’ feature always when configuring policies with governance actions. Supported governance actions depend on connected application API and vary between the applications.
Take these into account (list partly from docs.microsoft.com)
- File monitoring should be enabled in Settings. Go to Settings, and then under Information Protection, select Files. Select Enable file monitoring and then select Save.
- If there are no active file policies, then seven days after the last file page engagement time file monitoring will become disabled.
- If there are no active file policies, then 35 days after the last file page engagement time Defender for Cloud Apps will begin deleting the data that Defender for Cloud Apps maintains about these stored files.
- In general, when file scanning is enabled it will take hours or even longer before MDA has finished the scanning job
- O365 workloads (ODfb, SPO, EXO) detects malware-infected file very quickly (in minutes) but before the MDA malware detection policy kicks in, detecting the file & creates an alert can take hours
- If you have a custom policy that performs governance actions to the malware-detected file the latency is even longer (8-12 hours in my case)
- There isn’t any way to run MDA policies on demand so it’s not known when the policy exactly runs
- File Hashes is not included in the MDA alert details
- Updated 01/08/2022 – File hashes are now included for non-MS storage apps, SharePoint Online & OneDrive for Business
- I’m not a privacy expert but if you would like to use the ‘admin quarantine’ feature there might be a violation of GDPR in the EU area.
- ALL governance actions are found from MDA ‘Governance log’
Files shared into your connected storage apps by external users are handled as follows by Defender for Cloud Apps:
- OneDrive: OneDrive assigns an internal user as the owner of any file placed into your OneDrive by an external user. Because these files are then considered owned by your organization, Defender for Cloud Apps scans these files and applies policies as it does to any other file in your OneDrive.
- Google Drive: Google Drive considers these as being owned by the external user, and because of legal restrictions on files and data that your organization does not own, Defender for Cloud Apps does not have access to these files.
- Box: Because Box considers externally owned files to be private information, Box Global Admins cannot see the content of the files. For this reason, Defender for Cloud Apps does not have access to these files.
- Dropbox: Because Dropbox considers externally owned files to be private information, Dropbox Global Admins cannot see the content of the files. For this reason, Defender for Cloud Apps does not have access to these files.
Quarantine
- For a list of apps that support admin quarantine, see the list of governance actions.
- If a file in SharePoint or OneDrive is detected to be malware, it can’t be quarantined in the Defender for Cloud Apps portal. The file is already locked by SharePoint or OneDrive.
- Files labeled by Defender for Cloud Apps can’t be quarantined.
- Defender for Cloud Apps admin quarantine actions is limited to 100 actions per day. This limit can be increased with a support case.
Admin Actions – Authorizing files
When investigating detected files authorizing the file is possible (before governance action). What happens after authorizing is that MDA removes it from the malware detection report and suppresses future matches on this file.
Latency
As mentioned above, there is latency included in the detection. This table summarizes the findings:
| Activity name & time initiated | Detection time | Notes |
| User uploads potential malware file to O365 (ODfb/SPO) | Minutes after uploading to the service side | |
| MDA ‘Malware detection’ policy kicks in hours after the user has uploaded the file | This can take from 1 hour to 6 hours | |
| Governance action executed by MDA Policy name: Malware detected and moved to trash | Typically 10-12 hours before the custom policy kicks in and performs governance actions to the potential malware file. Governance actions demonstrated in this blog have the same latency times. | The file is already blocked by the O365 app and unusable by the end-user. If a user tries to download the file MDE blocks the download |
File Hashes – Updated 01/08/2022
In addition to file hashes available for malware detected in non-Microsoft storage apps, now new malware detection alerts will provide hashes for malware detected in SharePoint and OneDrive.