Updated 09/08/2018 with Central Mode Configuration, Kudos goes to my colleague @santasalojoosua
Last blog post I wrote, was about Security DevOps kit tool called AzSk. This tool can be used to scan Azure subscription and deployed components security settings among other functionality which tool has. The icing on the cake, you can send results from the security scan to Log Analytics workspace for further analyzes.
Today I go a step forward and automate the whole process. With this process, scan is performed automatically via Azure automation account and data will be send to Log Analytics workspace. Data can then analyzed via Log Analytics dashboard or directly from logs.
Pre-Requirements
Changes are needed to both Azure and Azure AD. Following permissions are needed to create objects:
- Service principal runtime account as a reader for subsciption
- Target Log Analytics workspace ID and shared key
Installation
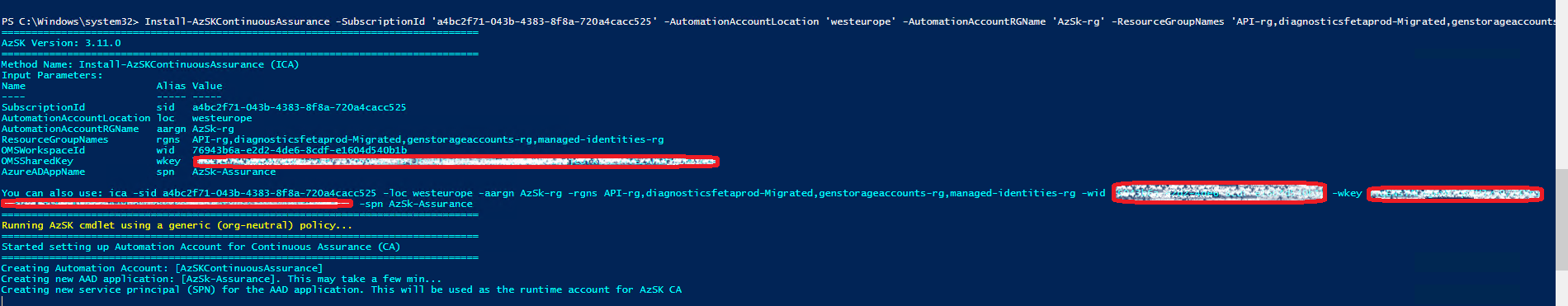
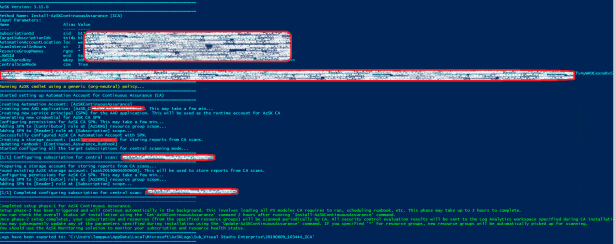
Installation is made through Powershell ISE with Azure account. Below is example script from my demo environment
#Import module
Import-Module AzSK
#Connect Azure
Login-AzAccount -Subscription a4bc2f71-043b-4383-8f8a-720a4cacc525
#Install Continous Assurance
Install-AzSKContinuousAssurance -SubscriptionId 'a4bc2f71-043b-4383-8f8a-720a4cacc525' -AutomationAccountLocation 'westeurope' -AutomationAccountRGName 'AzSk-rg' -ResourceGroupNames 'API-rg,diagnosticsfetaprod-Migrated,genstorageaccounts-rg,managed-identities-rg' -OMSWorkspaceId 'Insert your LA workspace ID here' -OMSSharedKey 'insert your own LA workspace key here' -AzureADAppName 'AzSk-Assurance'
Running the script
Verify Installation and Configuration
Confirm that all necessary components are properly configured. Available methods are from Azure portal or via Powershell.
PowerShell
Get-AzSKContinuousAssurance -AutomationAccountName <Account Name> -SubscriptionId <Sub ID> -AutomationAccountRGName >Resource Group Name>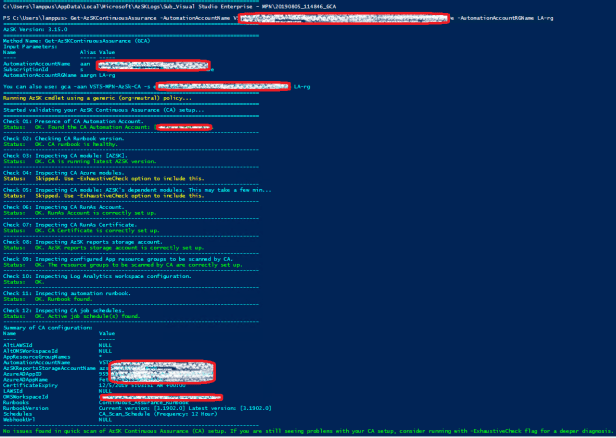
Azure portal
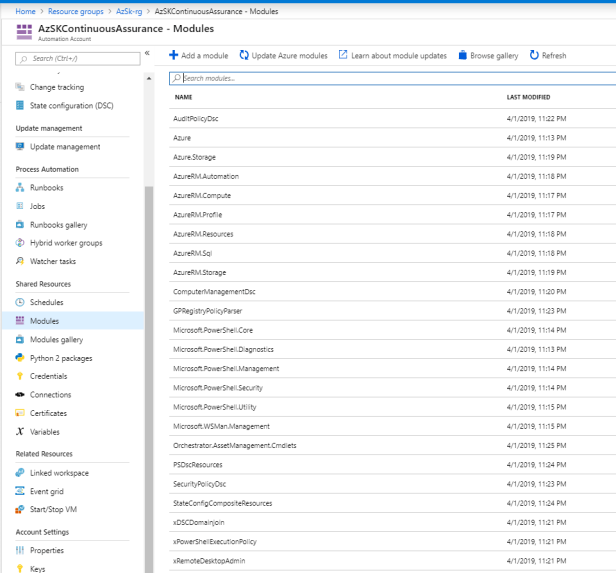
Verify creation of Azure Automation account named “AzSKContinuousAssurance“
Automation account settings
- Validate that Runbook “Continuous_Assurance_Runbook” is created
- Validate Schedule
- Validate Run Account which should contain newly created Azure AD application
- Validate PowerShell Modules availability
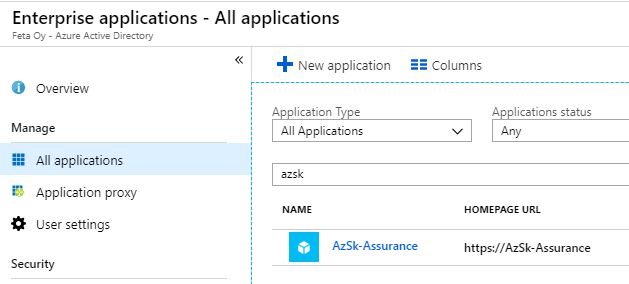
Azure AD Application created properly
- If you didn’t create application beforehand it’s named as “AzSk-Assurance“

Service Principal exists
- Check service principal from Azure AD Enterprise Apps blade
Permissions to Azure environment
- Installation adds automatically reader permission to subscription which is used to get services security information

Finally – verify CA Runbook execution and Log Analytics Connectivity
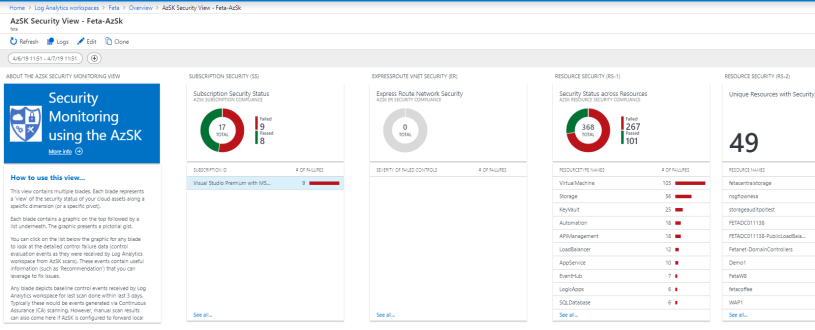
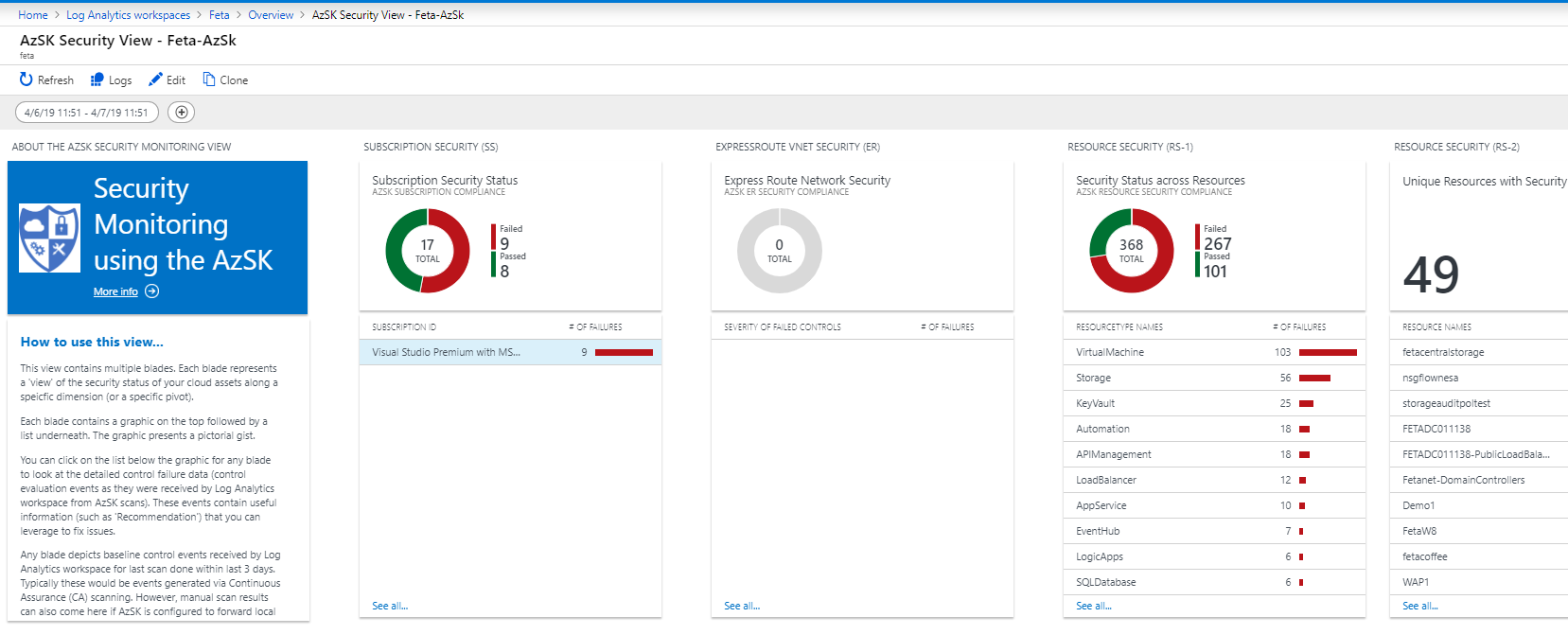
First, confirm that data is found from Log Analytics workspace. If you don’t have AzSk dashboard yet in your environment check my earlier post how to create it.
I can verify connectivity from Log Analytics dashboard and by making queries to Log Analytics data which shows definitely that I have everything in place as expected.
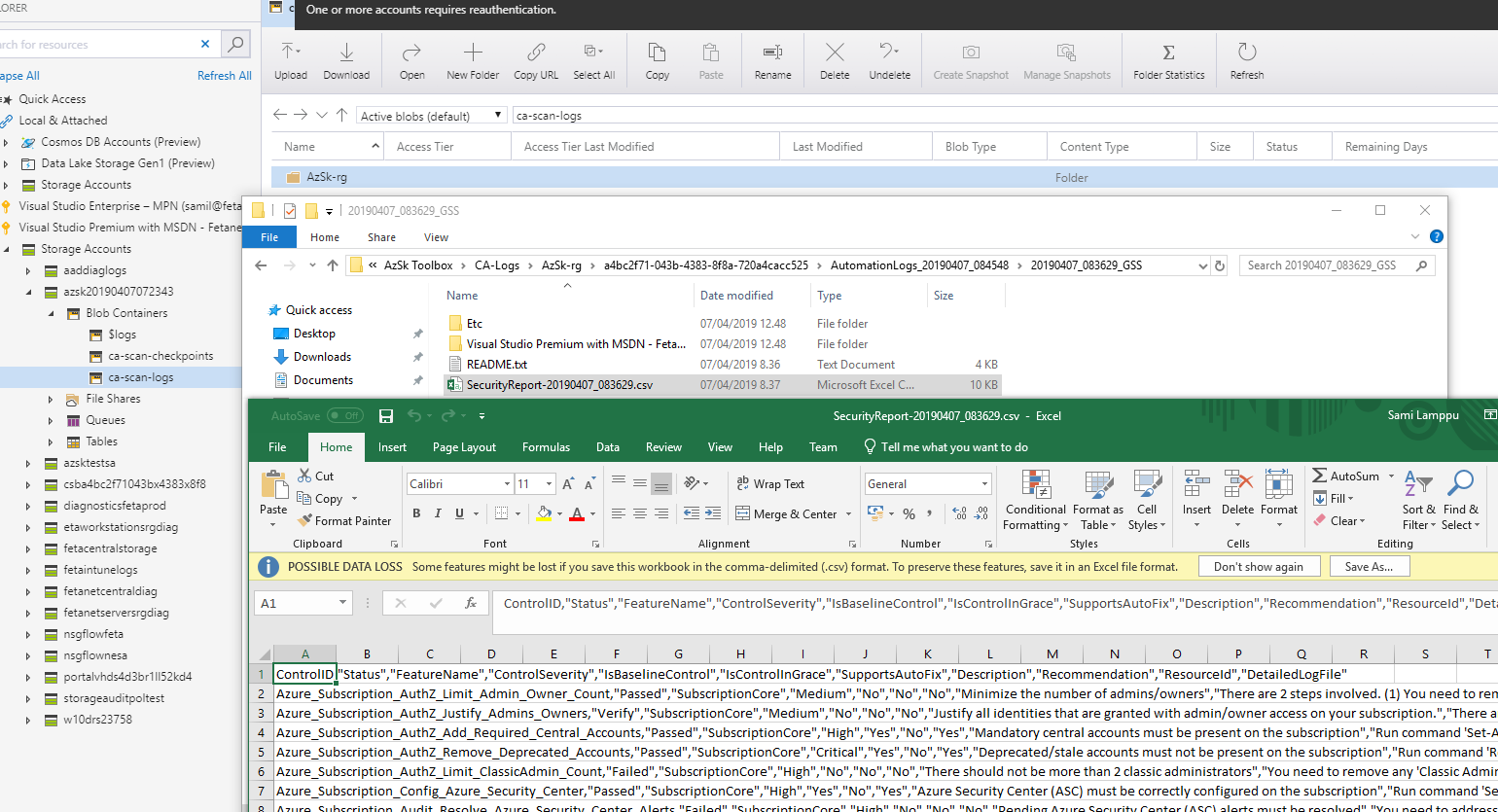
From storage account (azsk2019…) where data is also saved you can download csv files and analyze data on traditional way in case it’s needed.
Central Mode
If you have multiple subscriptions like many enterprises nowadays has, consider to configure subscription scanned by one automation account. Benefits:
- Single automation account in place
- Central location to manage automation account
- Central location for security data from all subscriptions
How to configure
When planning major changes to AzSK configuration I recommend to remove existing existing configuration before creating new one. I had Continuous Assurance in place and tried to update it to Central mode without success.
After removing current configuration and creating new central one it started to work immediately.
Following command contains all necessary and mandatory parameters for creating Central mode continuous assurance runbook.
$subs = <subid1, subid2>
Install-AzSKContinuousAssurance -SubscriptionId <Central sub Id> `
-TargetSubscriptionIds $subs `
-AutomationAccountLocation "westus2" `
-ScanIntervalInHours 2 `
-ResourceGroupNames "*"`
-LAWSId "Log Analytics Workspace ID" `
- LAWSSharedKey "Log Analytics Workspace Key" `
-CentralScanMode
Update Existing Configuration
If you need to update configuration, for example change the scan scope it can be done afterwards with Update-AzSkContinuosAssurance command.
What I did below, changed the resourcegroupnames parameter to ‘*’ which means that all resource groups from subsciption are in scope including all new ones.

Conclusion
With AzSk tool and automation you can easily get continuous security information from you environment to Log Analytics. This tool together with Azure Security Center (+ built-in audit policies) gives you quite good overall security information from audit perspective.
Next step is to strengthen Azure environment security posture based on audit data. Until next time!