Today we have quick post from the field about Seamless SSO key rollover.
Microsoft recommendation is to roll over Pass-throug Authentication Kerberos key on every 30 days. If it’s not done this will be found from the Azure AD portal. In near future you don’t need to perform any Powershell or scripting referring to Microsoft user voice “We are currently working on an approach that will allow Tenant Admins to do key rollover from the Azure AD portal; without the need for PowerShell or scripting”
The Case
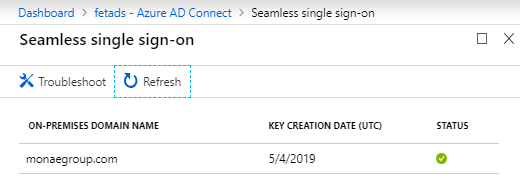
When using Seamless SSO Kerberos decryption keys needs to be re-enrolled for security purposes. At latest, when portal shows following warning it’s time to act.

Roll Over
Navigate to Azure AD Connect folder, import module and launch New-AzureADSSOAuthenticationContext cmdlet

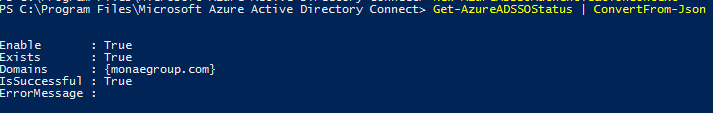
Before changing anything it might be good to confirm current status
Execute the commands
$creds = Get-credential
AzureADSSOForest -OnPremCredentials $creds
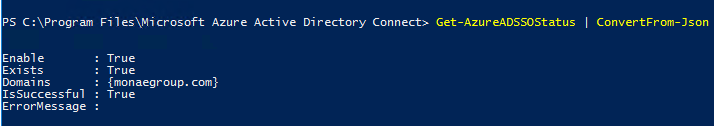
Get-AzureADSSOStatus | ConvertFrom-JsonVerify Changes
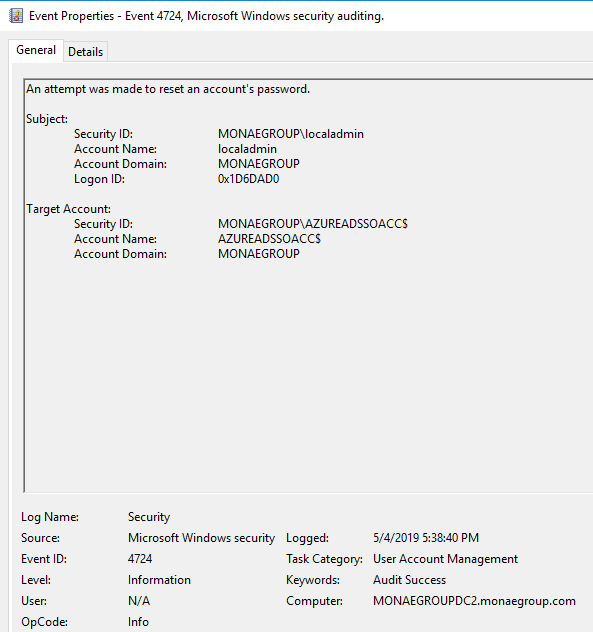
Open Domain Controller security log from Event Viewer and there should be following events from the change
- Event 4724 – attempt to reset account password
- Event 4742 – confirmation that computer account password was changed
- Verify status from Azure AD portal
More information from this link
How can I enroll Kerberos decryption key
Hope this helps!


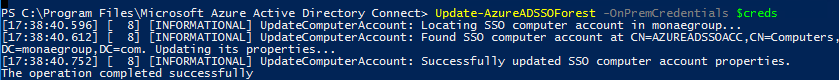

Thank you for the post! The right CMDlet to rollover the is
Update-AzureADSSOForest -OnPremCredentials $creds
Thanks for finding that one and giving feedback. I noticed that in picture command was correct. Now updated!
Hi, Will there be any user impact post kerberos Rollover which we should be aware about. Please advice
There are a couple of things I would like to highlight
1. Update the Kerberos decryption key on each AD forest that it was set it up on
2. The domain administrator account used must not be a member of the Protected Users group
3. Run it only ONCE. Otherwise, the feature stops working until the time your users’ Kerberos tickets expire and are reissued by your on-premises Active Directory.
Thank you very much. Very clear and easy to follow.
Thanks for the feedback!
Hey Sami,
You missed the “Update-” part at your command example. It has to be “Update-AzureADSSOForest -OnPremCredentials $creds”
Thank you for pointing that out. I will check and do necessary changes to the blog👍
Do we have to do this manually every 30 days? Can it not be automated?
Hi Steve,
Based on my knowledge you have to. 30 days is recommendation from MS side as they state in the ms docs “We highly recommend that you roll over the Kerberos decryption key at least every 30 days”.
https://docs.microsoft.com/en-us/azure/active-directory/hybrid/how-to-connect-sso-faq
As you can see, it’s also found from Azure user voice but no update in the last two years
https://feedback.azure.com/forums/169401-azure-active-directory/suggestions/33773926-automate-seamless-sso-kerberos-decryption-key-roll
what if I don’t update, would it have any negative impact?
In a nutshell, this reduces the risk of the Kerberos decryption key from being leaked. If it was to be leaked, a malicious user could impersonate Azure AD sign-ins for compromised users.
There aren’t any operational impacts if you don’t update it.