Azure Sentinel a cloud based SIEM by Microsoft which has been built a top of Azure Log Analytics. More fundamental information about product is found from links below
Microsoft official documentationB
How to Create Alerts in Sentinel
First things first, you need to get data from necessary data sources to Log Analytics workspace, which is underlying storage underneath Azure Sentinel. There are number of ready made connectors available and I encourage to check my earlier blog above how to configure the connectors.
When you have the connectors and data in place the fun begins, investigation and hunting.
Pre-Requirements
In my example I use “Security Events” as data source, which practically is Windows Server events from on-premises environment.
Confirm Azure Security Center Data Collection Settings
By the way, if you have wonder what’s the difference between Azure Security Center and Azure Sentinel I encourage to read this blog post.
To analyze the data it needs to be found from Log Analytics workspace which Azure Sentinel is using.
Open Azure Security Center – Security Policy and select correct subscription edit settings tab

Confirm data collection settings. Depends from your environment configurations where this one needs to be checked. Log Analytics agent for VMs can be deployed via Azure Policy, Deployment with ARM templates or via Azure Securite Center which is used in my case.
- Workspace name – this needs to be same than Sentinel is using
- Windows security events – common is enough in most cases

My Domain Controller is FETADC02 and when logged to DC itself I can verify that MMA agent is correctly connected to correct workspace. MMA is found from control panel.

Same result can be seen from Azure portal Log Analytics

Create Query and Investigate Case
Create Analytics Query
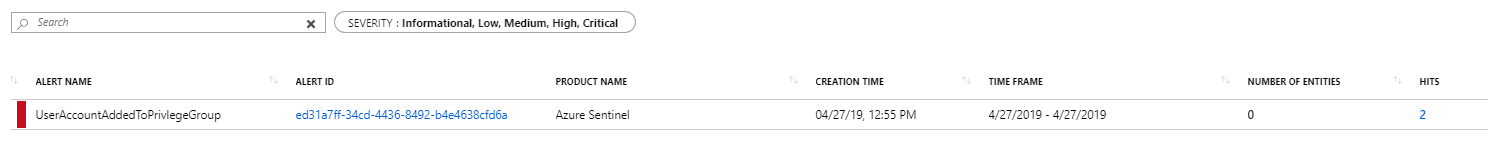
I did create alert rule which creates a case to Sentinel when user account is added to a privileged built in domain local or global group such as the Enterprise Admins, Domain Admins, etc.
The configuration is made from Configuration – Analytics tab.
GitHub link to Privileged Group example case
GitHub link to Azure Sentinel repo
Investigate Case
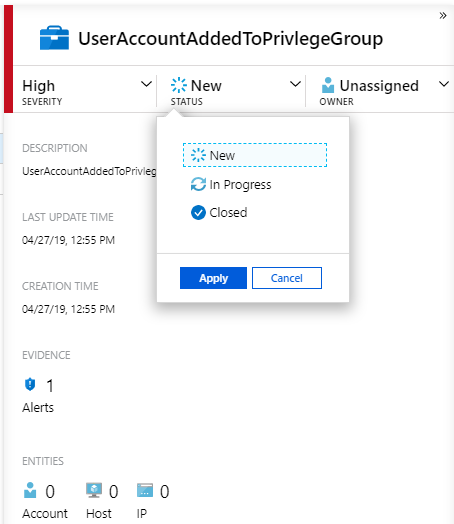
When user is added to high privileged group in on-premises Active Directory and Log Analytics Agent has send data to the workspace the case will be created to Sentinel dashboard. Following actions are available for investigation:
- Assign case status
- Assign owner for case
- Further investigation through investigate dashboard
- View Full details from the case which allows you to view all information and playbooks from case
- Playbooks helps to create automated action for a case. In example below I’m sending an email when such case is created.
Summary
I have been fortunate to have opportunity to work with Azure Sentinel with two of my customers. It will definitely help enterprises to make them environments more secure at the future.