The first Microsoft Cloud App Security case in 2020 is all about Microsoft Cloud App Security (MCAS) controls & monitoring with Power BI. This blog post highlights notes from our experience where I had a pleasure to work with my awesome colleague @pitkarantaM.
The Case
Once upon a time, there was a huge corporation where one business unit wanted to protect Power BI usage with Microsoft Cloud App Security (MCAS). Use cases and scenarios (highlighted ones) were defined as follows:
- Manual and automatic classification of Power BI content with Azure Information Protection
- Control Power BI content download based on device status (managed / unmanaged) and document classification (AIP labeling & protection)
- Control Power BI content copy, paste and print actions based on device status
- Get all possible alerts from MCAS to relevant SOC team
Pre-Requirements
Using Cloud App Security with Power BI is rarely a new capability and a reference document is found from docs.microsoft.com. I also encourage to read Power BI sensitivity labels article. When planning MCAS and Power BI integration, take into consideration that:
- Sensitivity labels can be applied only on dashboards, reports, datasets, and dataflows
- Label and protection controls enforcement on exported files are supported only for Excel, PowerPoint and PDF files.
- Label and protection are not enforced when data is exported to .CSV files, Subscribe to email, Embed visuals and print
I’m not going through all the necessary configuration details here from the environment. What’s needed in a nutshell in our case are:
- Unified Labeling
- The Conditional Access policy for sessions control
- Power BI Azure Information Protection integration
- O365 Unified Audit Log enabled
- MCAS – O365 & Azure API integrations
- MCAS – Files scan enabled from settings
Cloud App Security Policies
This chapter summarizes our experience from the four uses cases defined above.
Use Case 1 – Manual or Automatic Classification of Power BI content with Azure Information Protection (AIP)
Power BI supports Azure Information Protection, integration needs to be configured in place before it can be used.
Based on our tests, manual classification works as expected and end-users are able to classify content in Power BI based on pre-defined Azure Information Protection (AIP) classifications and current feature limitations mentioned above.
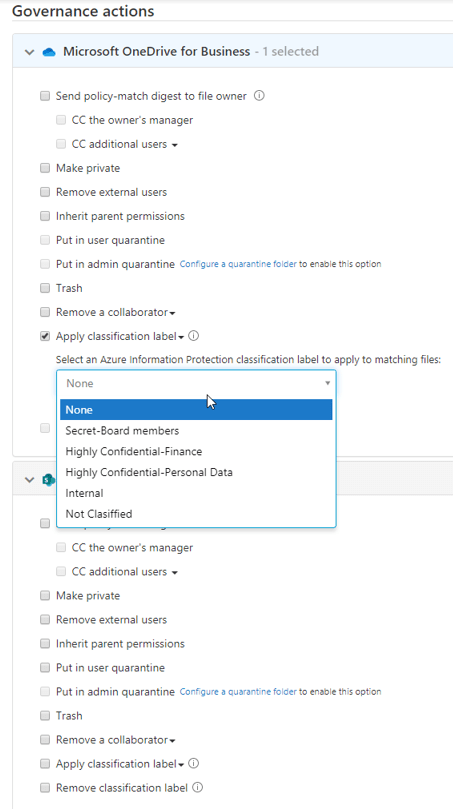
Automatic AIP classification doesn’t work at the time of writing with Power BI. Currently, MCAS supports AIP governance actions for OneDrive and SharePoint from Microsoft workloads. From 3rd party applications, Box and G Suite are supported for AIP governance actions. A full list of supported actions and applications can be found from this link.
Use Case 2 – Sharing Power BI Content To Externals
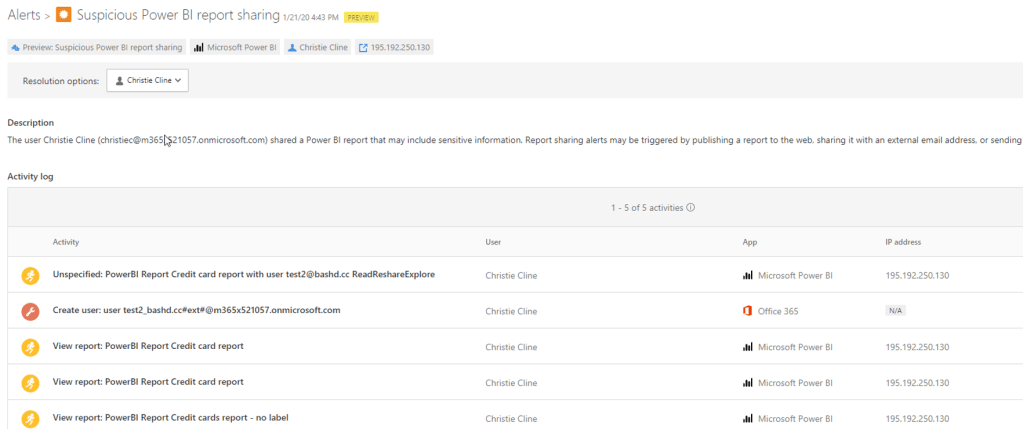
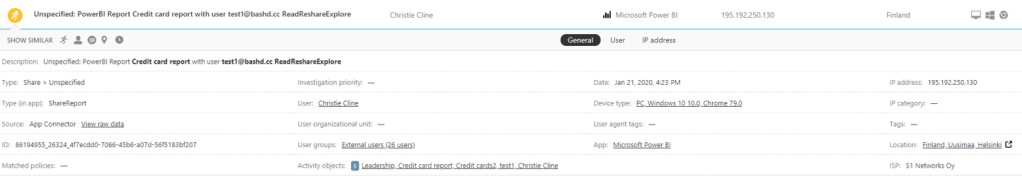
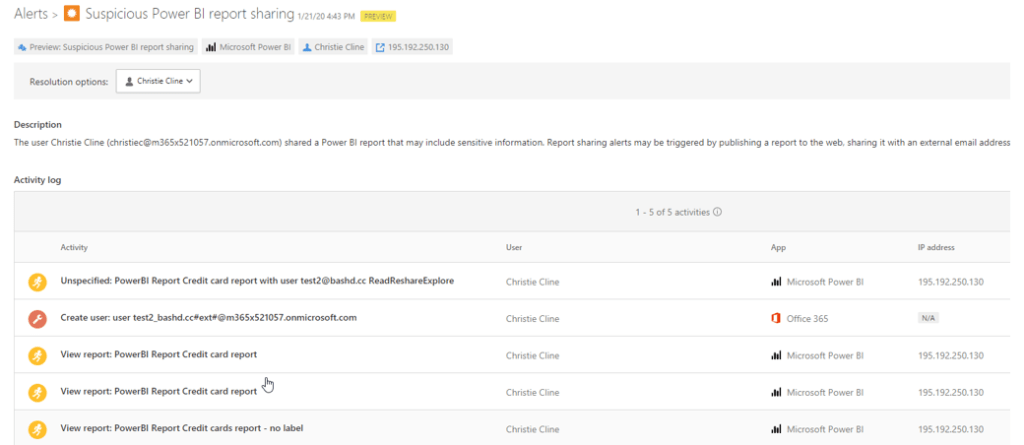
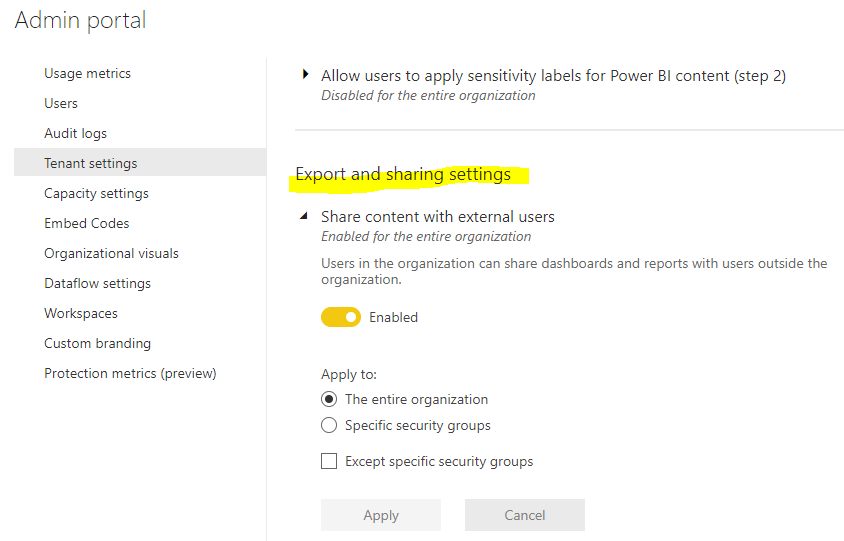
It’s not possible to block the sharing of Power BI content to external users by Microsoft Cloud App Security controls. What you can achieve, is alert to MCAS if someone shares material to outside of your organization.
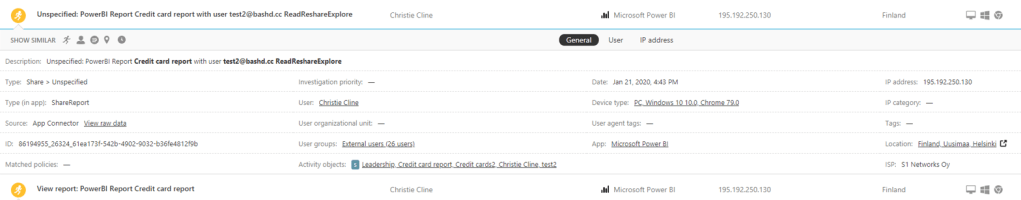
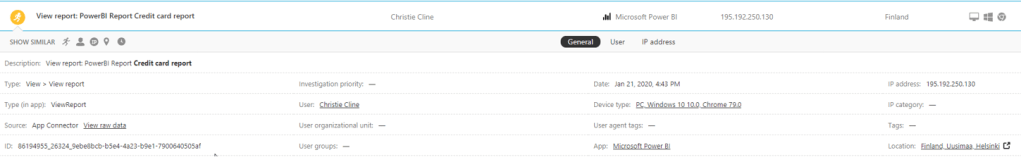
Worth to mention is, this activity can be viewed from the Activity Log which gets its data from O365 API and from the Unified Audit Log (UAL). Microsoft documentation says that events should be delivered in 30min time frame to UAL log but in our demo tenant, it took a couple of hours in some cases.
If you want to block external sharing totally from Power BI, it’s possible from Power BI tenant wide settings.
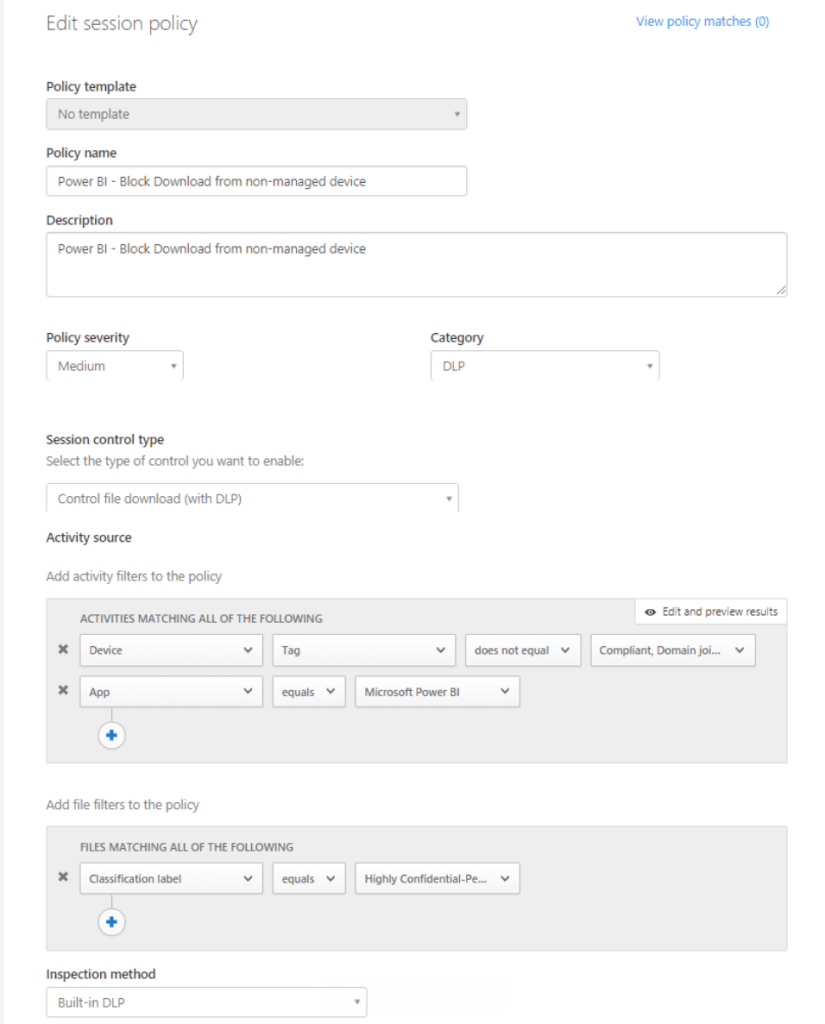
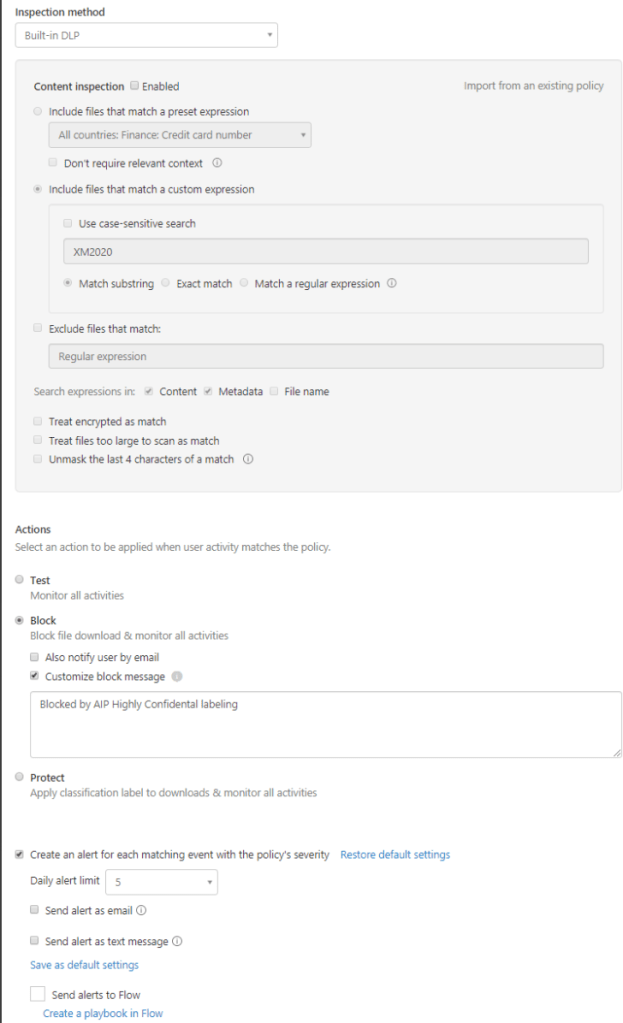
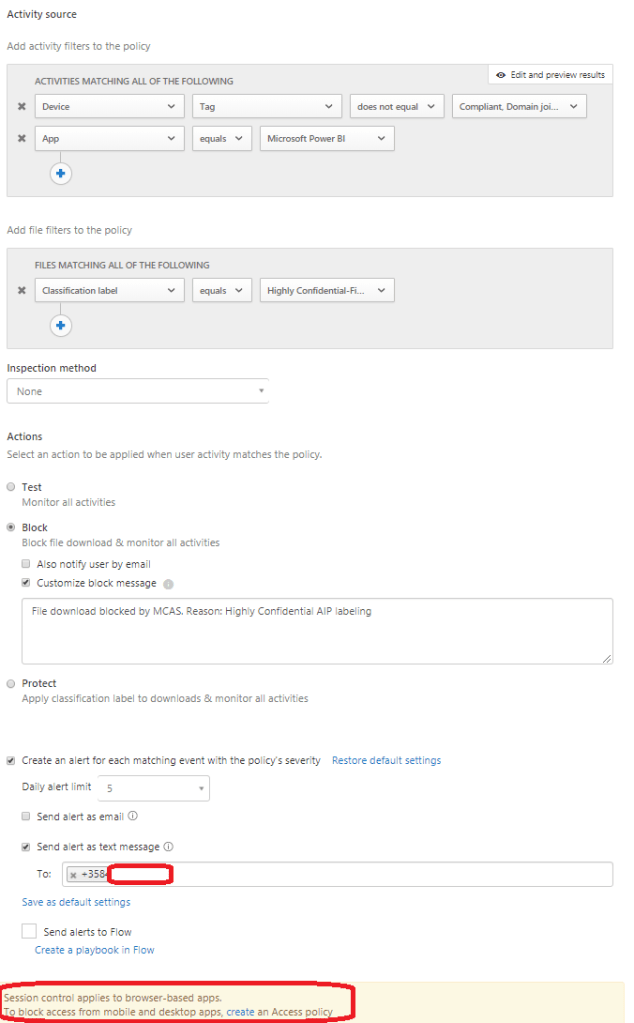
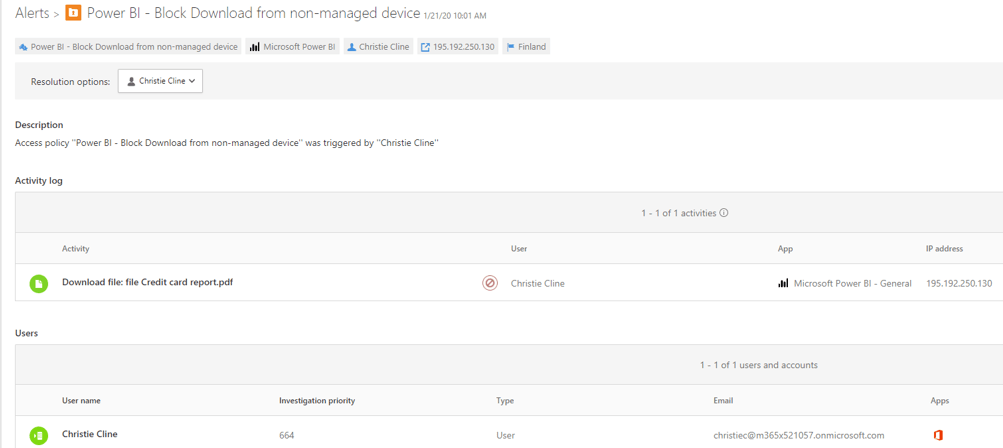
Use Case 3 – Download Block Based on Device Location + AIP Classification
The idea in this use case was to control (block download) of the Power BI content based on device status and AIP classification. With this policy, you can block download activity if controls are not satisfied. In this policy used controls are:
- Device is Domain Joined (HDJ) or Intune Compliant
- App is Power BI
- Classification label is Highly Confidential or Confidential
These controls works with both, PDF & PPT with exports.
Note: the Same restriction than in Conditional Access Policies applies in here, device status which can be used are: Hybrid Device Join & Intune Compliant device. The AAD Join device without Intune enrollment doesn’t set device status to ‘compliant’ and the device isn’t recognized by MCAS.
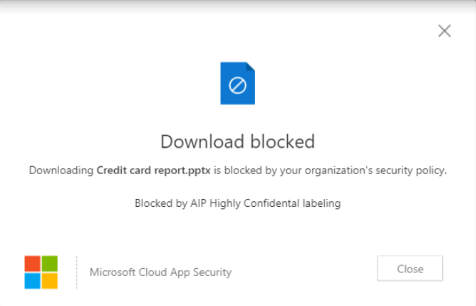
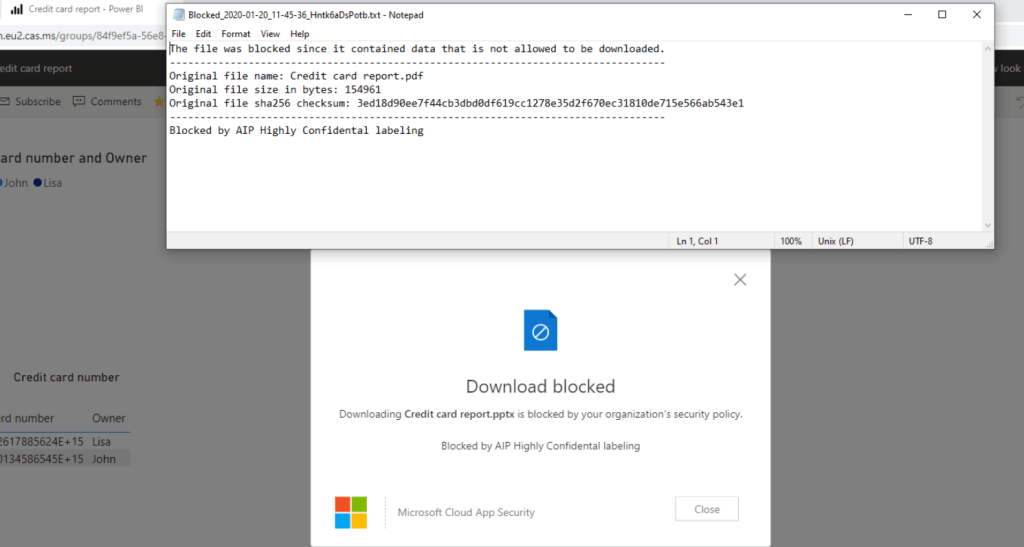
End-user experience is something like this
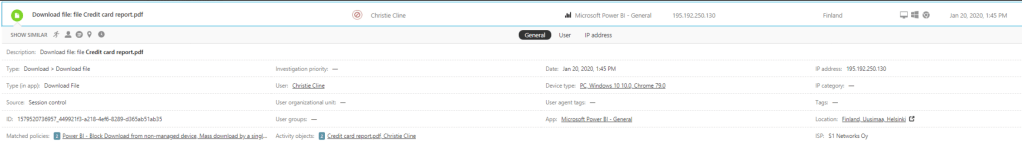
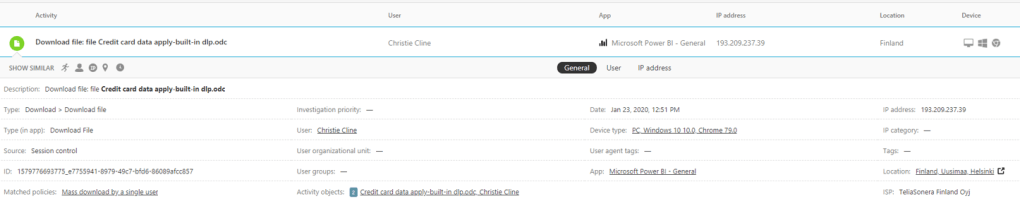
Cloud App Security admin can start investigation from the alerts.
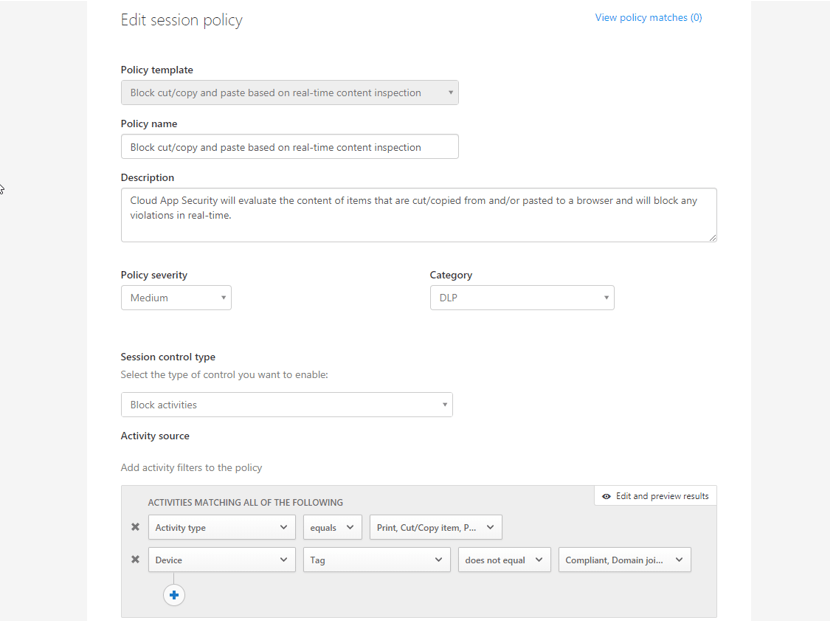
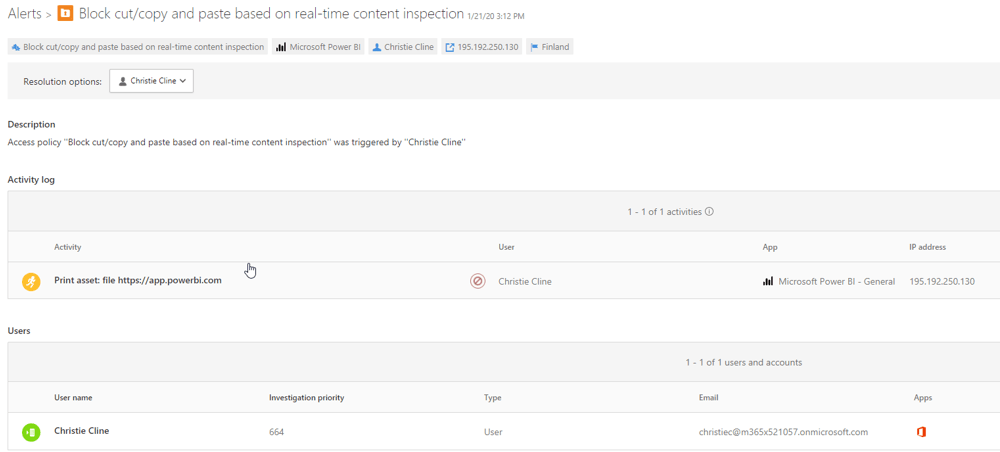
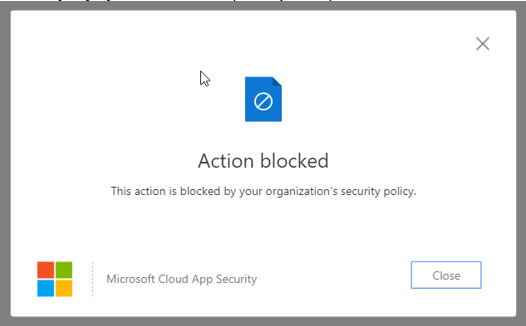
Policy 2 – Block cut/copy and paste based on real-time content inspection
With this policy we want to control activities during the session. Settings configured:
- Device identification
- App identification – only Power BI is targeted
- Activity type – Print, cut/copy, paste item
- Classification in DLP section
- Activity – block
Take into account that this affects only to browser based connections, native clients and API connections are not controlled by this policy.
When user performs the action which is blocked pop-up will appear.
Monitoring
All of the actions described in earlier chapters will generate an activity log event or alert to Cloud App Security for further investigation.
Activities
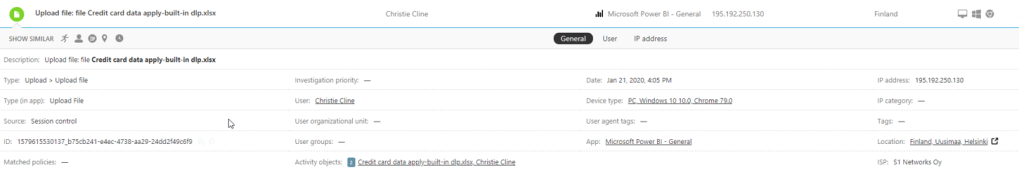
Following activities were found from the Activity Log during tests
- User downloads file which contains credit card data in excel
- User opens a report
- User shares are report
- User uploads a dataset
- User prints a report
Alerts
The following alerts were created to Microsoft Cloud App Security during test period
- Suspicious Power BI report sharing
- Prevent copy/paste on real-time content inspection
- Mass download
- Prevent user to download content from non-managed device
Summary
Microsoft Cloud App Security development pace has been breathtaking during the last couple of years and for a reason, it’s in the top right corner in the Gartner Quadrant report for Cloud Access Brokers.
It’s for sure, the best tool in the Microsoft ecosystem to monitor internal users’ suspicious behavior. To get most out of it I highly encourage to make integrations to Microsoft Defender ATP & Azure ATP to combine identity information from on-premises and cloud together with device information to the same security solution.
Activity controls are not so widely used (at least yet) and those definitely need extra attention. What I mean by this, for example with Power BI you have session controls available for any browser on any major platform on any operating system but MCAS doesn’t have the ability to control Power BI public API or native client connections. There are ways to protect these connections (Conditional Access, Intune) but whiteboard might be needed to evaluate how to configure your infrastructure as bulletproof in every scenario.