Microsoft Cloud App Security (MCAS) integrations with app connector are super easy to establish. At time of writing, the supported sources are:
- Azure
- AWS
- Box
- Dropbox
- GitHub
- GPC
- Office 365
- Okta
- Salesforce
- ServiceNow
- Webex
- Workday
App connectors use the cloud provider’s own APIs to establish visibility and control through Microsoft Cloud App Security to the apps the organization is using.
According to Microsoft: Microsoft Cloud App Security leverages the APIs provided by the cloud provider. Each service has its own framework and API limitations such as throttling, API limits, dynamic time-shifting API windows, and others.
Taking into account different limitations services impose on the APIs, the Cloud App Security engines use the allowed capacity. Some operations, such as scanning all files in the tenant, require numerous APIs so they’re spread over a longer period. Expect some policies to run for several hours or several days.
In this blog I demonstrate how to connect ServiceNow to MCAS.
Pre-Requirements
Naturally, Microsoft Cloud App Security instance and Service Now instances are required. For testing purposes, you can create a dev instance from https://developer.servicenow.com/dev.do.
Take into account that Cloud App Security supports the following ServiceNow versions:
- Eureka
- Fiji
- Geneva
- Helsinki
- Istanbul
- Jakarta
- Kingston
- London
- Madrid
- New York
- Orlando & Paris (published 2020) are not officially supported.
In order to connect ServiceNow with Cloud App Security, you must have the role Admin in ServiceNow and make sure the ServiceNow instance supports API access.
Connectivity
Before establishing a connection from MCAS to ServiceNow, configurations described in the next chapter are needed in the ServiceNow side.
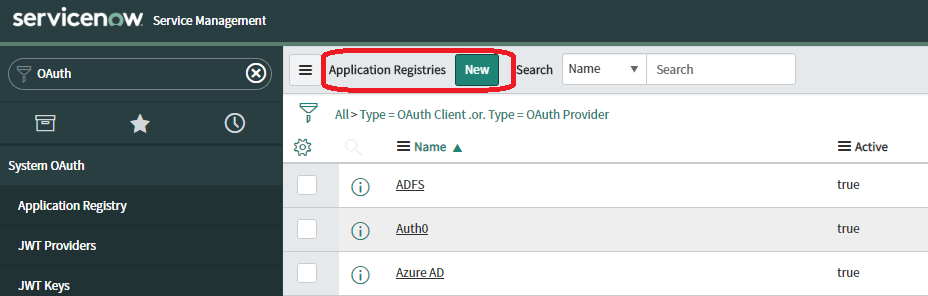
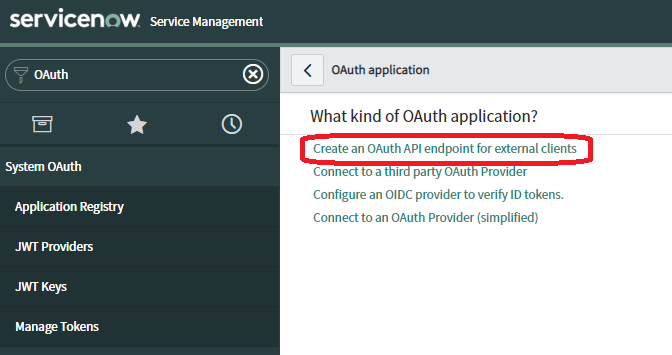
ServiceNow
- Create new OAuth profile for external clients
- Increase “Access Token Lifespan” to at least 3600
- Copy needed OAuth profile values after profile is created – these are needed in the MCAS side
Cloud App Security
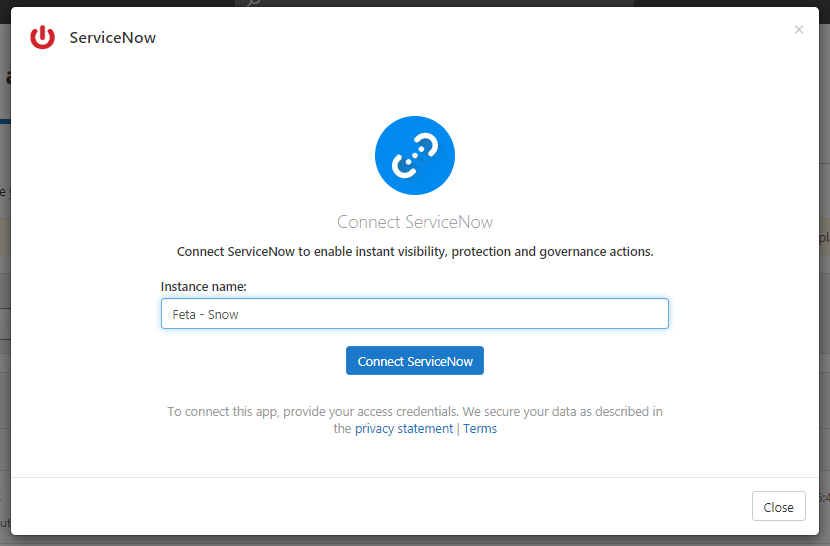
In MCAS side, add ServiceNow from the App Connector config with values copied from the Snow side.
Next Steps
ServiceNow is now connected, what’s next?
ServiceNow might contain a large amount of sensitive information such as customer information, process information, information about incidents, and possibly reports that contain sensitive information about the organization. For that reason, it’s important to protect ServiceNow, lets see how Cloud App Security can help here.
Main Threats According To Microsoft
- Compromised accounts and insider threats
- Data leakage
- Insufficient security awareness
- Ransomware
- Unmanaged bring your own device (BYOD)
How To Detect Anomalies
These built-in policies are enabled out of the box and the policies covers any app that’s integrated to MCAS:
| Type | Name |
| Built-in anomaly detection policy | Activity from anonymous IP addresses Activity from infrequent country Activity from suspicious IP addresses Impossible travel Activity performed by terminated user (requires AAD as IdP) Multiple failed login attempts Ransomware detection Unusual multiple file download activities |
| Activity policy template | Logon from a risky IP address Mass download by a single user Potential ransomware activity |
How to Protect Sensitive Information
These templates are available if you want to create a custom policy but not enabled by default. More information about the “Data Protection Policies” is found here.
| File policy template | Detect a file shared with an unauthorized domain Detect a file shared with personal email addresses Detect files with PII/PCI/PHI |
File Policy Detections
One huge advantage in Cloud App Security is native API connections where MCAS can enforce a wide range of automated processes using the provider API. Such cases could be: continuous compliance scans, legal eDiscovery tasks and DLP for sensitive content shared publicly.

When using monitoring mode (not enforcing access through MCAS proxy) you will benefit from the activities that cloud provider API provides. From the activities ingested to MCAS you can create alerts.
Governance Action
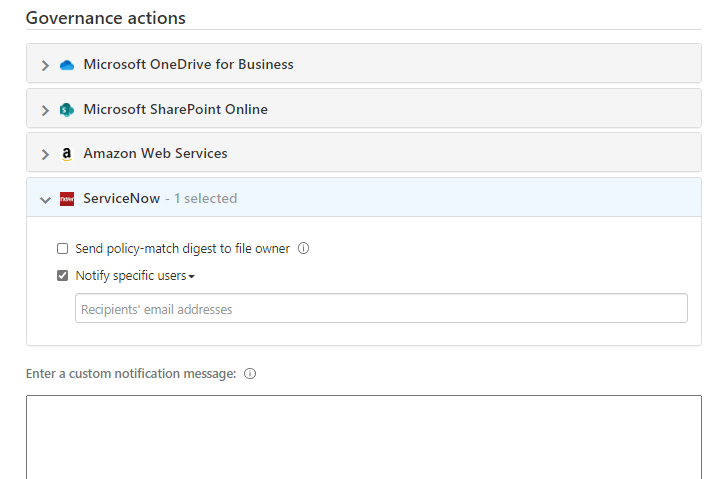
Using an MCAS proxy between the governance actions can be enforced through API. These actions depend naturally on the App and API and because remediation actions use the cloud provider APIs, actions might vary from one app to another. Here you can find a full list of file governance actions. Unfortunately, for ServiceNow, only the following actions are available:
- Send policy-match digest to file owner
- Notify specific users
Troubleshooting
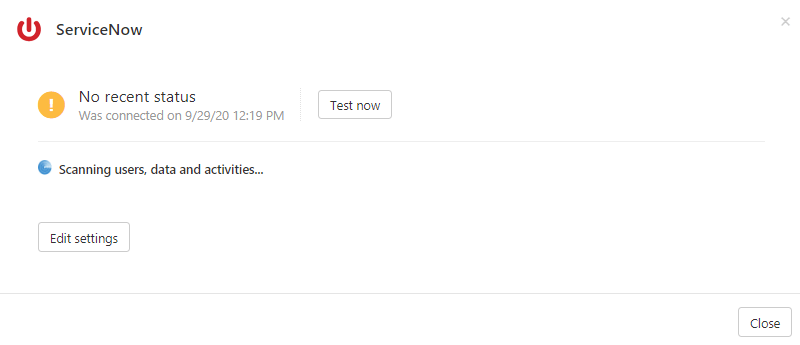
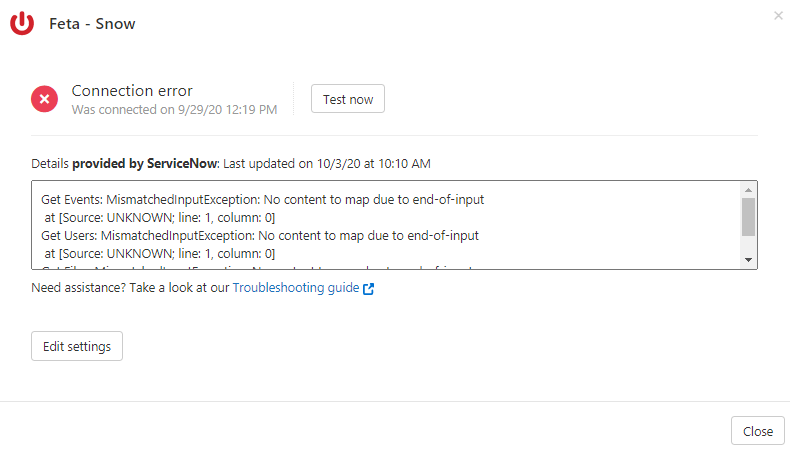
In case you disable the ServiceNow admin account that has been used to create the initial connection the following error might be shown in the MCAS portal. If that’s the case – enabled the ServiceNow account. The documentation states that this account is only used when establishing the initial connection but based on my experience this account needs to be enabled.
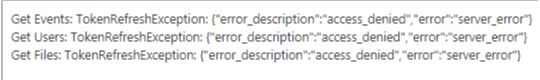
If ServiceNow instance is being hibernated you will receive the following error. I’m using ServiceNow developer instance and it seems that if there isn’t any activity it’s being automatically hibernated. Wake the instance and connection should be alive in a couple of minutes.