Cyberattacks have become increasingly sophisticated in the ways they exploit the apps organization have deployed in on-premises and cloud infrastructures, establishing a starting point for privilege escalation, lateral movement, and exfiltration of your data (link).
For that reason, monitoring of application behavior in cloud environment is crucial. One example of such attacks, where applications are leveraged, is ‘Illicit consent grant’ attack.
Consent Grant is the perfect tool to create backdoors, and MFA bypasses in the victim’s environment. There are two scenarios for attacker to pursue targeting individual users; Individual consent grants for non-admin permissions, and/or targeting admins for requiring permissions that only admins can grant.
Both scenarios allow data exfiltration, while the latter also offers perfect backdooring entry (App permissions for multi-tenant app).
“In an illicit consent grant attack, the attacker creates an Azure-registered application that requests access to data such as contact information, email, or documents. The attacker then tricks an end-user into granting that application consent to access their data either through a phishing attack or by injecting illicit code into a trusted website. After the illicit application has been granted consent, it has account-level access to data without the need for an organizational account.
Normal remediation steps, like resetting passwords for breached accounts or requiring Multi-Factor Authentication (MFA) on accounts, are not effective against this type of attack since these are third-party applications and are external to the organization. These attacks leverage an interaction model that presumes the entity that is calling the information is automation and not a human.”
More information about the attack, detection and remediation found from our community project – Azure AD Attack & Defense Playbook & Microsoft 365 Defender Threat Intelligence Team blog.
App Governance together with MCAS & Azure AD provides platform that can be used to detect suspicious activities from the applications.
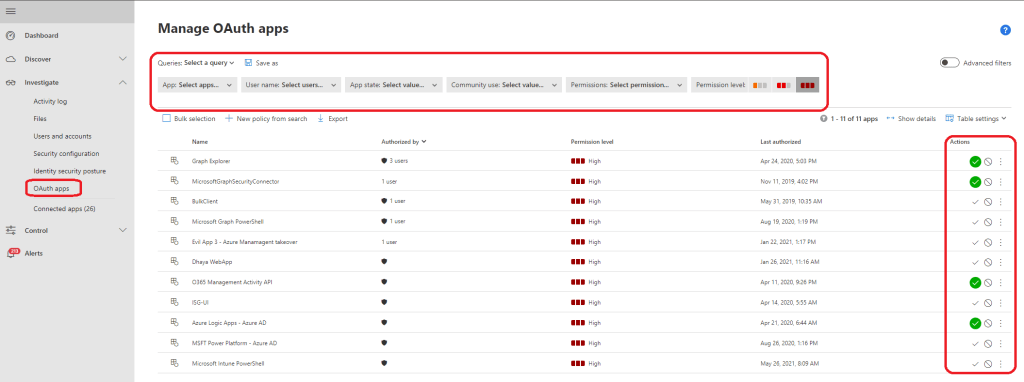
Cloud App Security – OAuth Applications
Before App Governance in Microsoft Cloud App Security (MCAS) was introduced MCAS has offered a way to investigate applications directly from MCAS console. This feature still exist and haven’t disappear anywhere and actually it’s used in App Governance together with Azure AD provided data. So, if you still want to use ‘Investigate – OAuth’ blade, nothing prevents you to do so.
App Governance – MCAS add-on
What’s ‘App Governance’? Based on Microsoft: ‘It’s a security and policy management capability that customers can use to monitor and govern app behaviors and quickly identify, alert, and protect from risky behaviors with data, users, and apps. App governance is designed for OAuth-enabled apps that access Microsoft 365 data via Microsoft Graph APIs‘.
You read right, it’s an add-on capability for MCAS located in compliance.microsoft.com portal. You naturally need proper MCAS license (+ AppG add-on license) to use the feature.
Architecture
How does App Governance work, and how it collects data? Data is collected from different data sets such as Azure AD & Cloud App Security, the App Governance collect information and provides the data in a single pane of glass in compliance center (compliance.microsoft.com). Even though, it’s MCAS addon the actual portal is not in MCAS, it’s in compliance center.
Side note: App Governance alerts are sent to MCAS, but not to M365D by design. Vice versa, MCAS alerts are sent to App Governance.
Configuring
Microsoft docs has good guidance how to enable and configure the feature. Pay attention to the following topics:
- You need license for App Governance – MCAS or M365 E5 license is fine
- You need to activate the Add-on separately
- After enabling the integration, verify that newly created policies exists in MCAS
- Know issues – bi-directional sync doesn’t work with M365 Defender
In my environment, all App Governance policies were not created when I enabled the integration. Based on the documentation, 7 policies should found (pic on the left) from MCAS but I only found policies that stated with the name ‘Microsoft 365 …’
Leveraging the Capabilities
Visibility and Insights
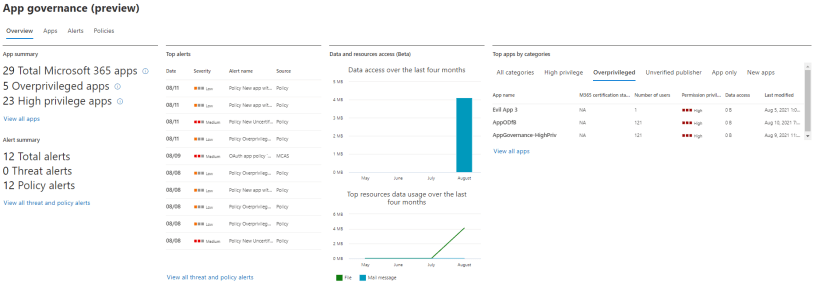
App Governance provides great overall status page to the M365 environment OAuth applications that access data via Graph API. Based on MS documentation it provides the following features:
- A high-level summary of the third-party and Line of Business apps in your Microsoft 365 tenant.
- Alerts based on the violation of any pre-configured policy and/or detection of any anomalous app behavior.
- Quick insights into apps that do not use one or more permissions they have been granted (Over-permissioned).
- Apps that have powerful permissions that allow data access or a key setting in the tenant (High privileged).
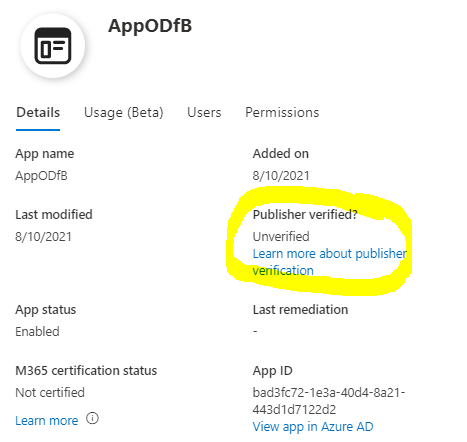
- Apps that do not have a verified publisher (Unverified).
App Access and Usage
It provides richer information about the application than MCAS OAuth app blade alone, such as:
- Usage details
- Users
- Publisher and is publisher verified
- App permissions
The data provided by App Governance is useful when evaluating application usage and permissions. Same possibility, “disabled app” exist also in App Governance comparing to MCAS OAuth blade.
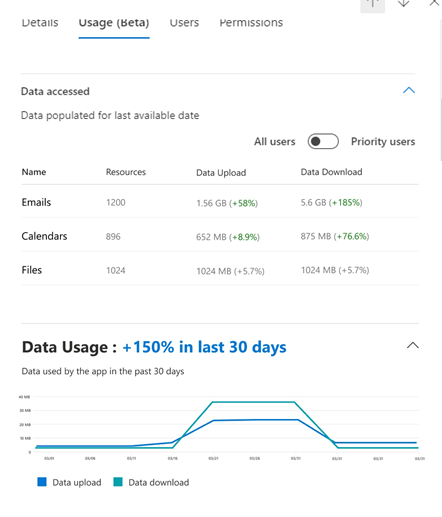
The last picture is from Microsoft TechCommunity announcement, where is seen very useful “App Usage” details, how much data has been download/uploaded and number of resources.
Policies
In pp Governance you have possibility to create polices based on an app policy template or create custom policy. The available built-in template categories and templates are:
- App users and data access
- New app with a high volume of data access
- App permissions
- Overprivileged apps
- New app with high-privilege permissions
- M365 certification
- New uncertified app
- Custom policies
- Custom policies have 17 conditions available at the time of writing if built-in policies doesn’t fit to your scenario
When creating policies keep in mind policy status options:
- Audit mode: Policies are evaluated but configured actions will not occur. Audit mode policies appear with the status of Audit in the list of policies.
- Active: Policies are evaluated and configured actions will occur.
- Inactive: Policies are not evaluated and configured actions will not occur.
Example process for creating new policy by Microsoft
Detection and Remediation
I have seen in many environments that number of alerts & incidents might be overwhelming. For that reason pay attention to policy detections and automation. The latter one is key-factor to success in security monitoring. App Governance offers (together with MCAS & AAD) possibility to automatically remediate alerts through the action settings on active app policies.
Bi-directional sync exists between the solutions which helps remediation part. In public preview alerts resolved in Defender will have to be manually resolved in app governance as well.
Test Drive
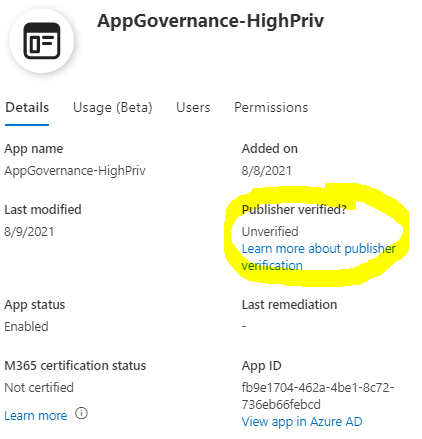
In my environment I have two (2) applications named: AppGovernance-HighPriv & AppODfB. When these applications were registered to Azure AD, AppG identifies immediately that these apps are not from verified publishers. For some reason, only ‘Graph Explorer’ is identified as Microsoft application.
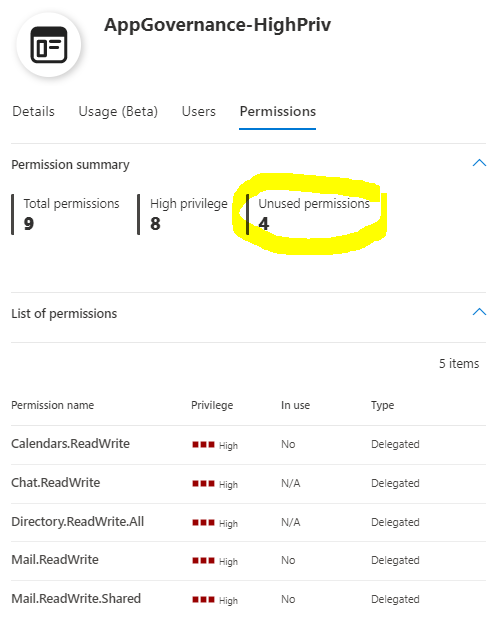
AppG identifies the app permissions and also unused permissions from the app. This data is used to identity are the permissions used or is application overprivileged.
If app doesn’t have any consented users it’s listed as ‘App only’ in overview page
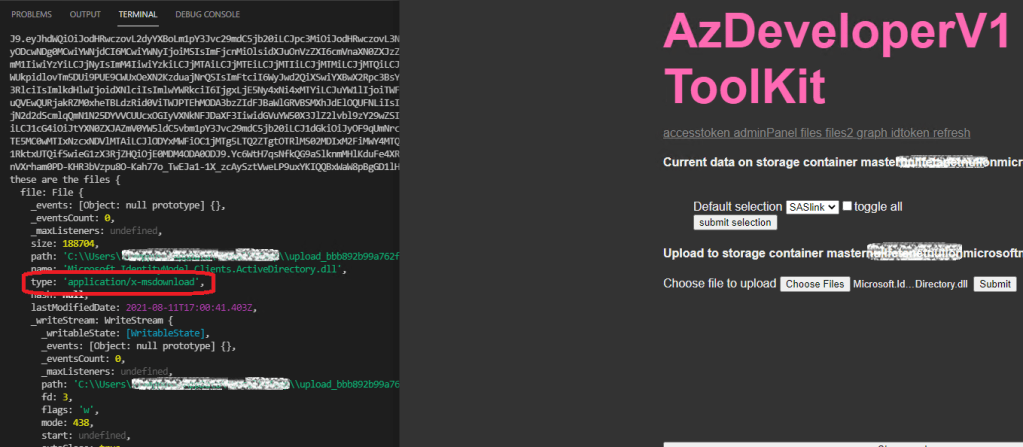
My fellow and always helpful MVP, Joosua Santasalo helped me and we created (not so fancy but useful) application to push data through Graph API to test how AppG is able to detect the applications. Keep in mind that for now, only traffic through MS Graph to EXO, SPO & Teams activities are logged and activities to Azure AD are not. This is not mentioned in the documentation and this assumption is based on the tests I made.
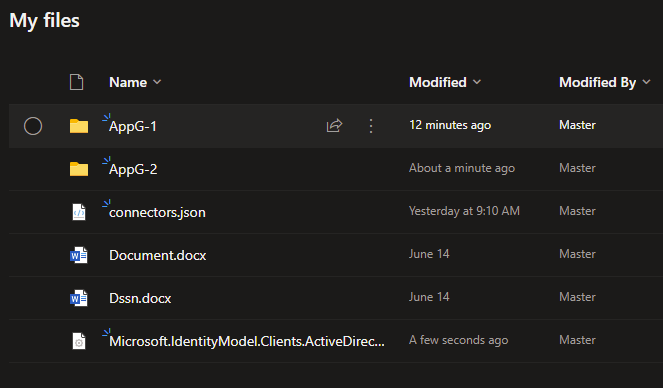
As you can see from below, I used demo app to call MS Graph and upload files to OneDrive for Business.
Caveats
- Anomalous activities from Azure-only apps that are not granted permissions to access Microsoft 365 resources are not included in app governance detection and alerting
- Based on tests made it seems that only activities from Teams, EXO & SPO are logged and analyzed in data consumption
- For example, Azure AD user identity changes through MS Graph are not seen here
- I had problems with the App details page showing all “Usage” details from the apps.
- Transactions in my test were relatively small and don’t have detailed information how often dashboards are updated
- Updated 08/18/2021 – data access and usage works now as expected in my environment
- Verify that all policies mentioned in the docs are created to the environment (tested in two different environments and I didn’t see all of them)
- Anomalous activities from Azure-only apps that are not granted permissions to access Microsoft 365 resources are not included in app governance detection and alerting
- App governance sends its alerts as signals to Microsoft Cloud App Security and Microsoft 365 Defender for more detailed analysis of app-based security incidents
- In my environment I have had problems with alert sync. Evaluation is still in progress and I’ll update the blog when have more information to share
- Updated 08/18/2021 – There was identified problems in the backend sync that is now fixed by the Product Group. I needed to re-enable the AppG integration in MCAS settings (see pictures below).
- 2-way sync between Microsoft Defender and app governance alerts – currently alerts resolved in Defender will have to be manually resolved in app governance as well
Summary
App Governance (AppG) offers a way to monitor OAuth-enabled app behaviors and detect malicious activities. It provides more granularity than MCAS alone and if you have licenses already in place I recommend to activate the solution. In my opinion, it would have been natural to add AppG in part of MCAS but it’s found from compliance center (compliance.microsoft.com) where all compliance related information is stored.
Keep in mind that the feature is still in public preview. In general, it looks very useful addition to Microsoft security solutions stack to detect suspicious app behavior, manage and govern apps in cloud environment.
References
Public Preview of App Governance
Create App Governance policies
App Governance Detection & Remediate
Azure AD Attack & Defense Playbook – Illicit Consent Attack
Microsoft delivers comprehensive solution to battle rise in consent phishing emails