Imagine the scenario where business critical data leaks out from the organization to unmanaged cloud application. Or suddenly, there are growing number of users using an application that is considered ‘high risk’ app based on app reputation.
In both scenarios, Microsoft Cloud App Security (MCAS) can save your day to detect both activities and further admin can block access or set controls to the application.
Side note: New feature, called App Governance, provides an additional layer for protecting and detecting possible malicious OAuth applications that access Microsoft Graph API.
In this blog I will cover possibilities for app management and continuous monitoring. If you want to get yourself familiar with the Cloud App Security ‘Cloud Discovery’ feature, I encourage to read my Tech Community blog post about it (published Feb/20).
Discover and Manage Shadow IT in your environment
With Cloud App Security ‘Cloud Discovery’ feature organizations can identify applications and user activities, traffic volume, and typical usage hours for each cloud application. In a nutshell, to detect Shadow IT and possible risky applications.
Side note: Based on Microsoft’s reports, an average organization uses more than 1000 applications that are not controlled by IT department.
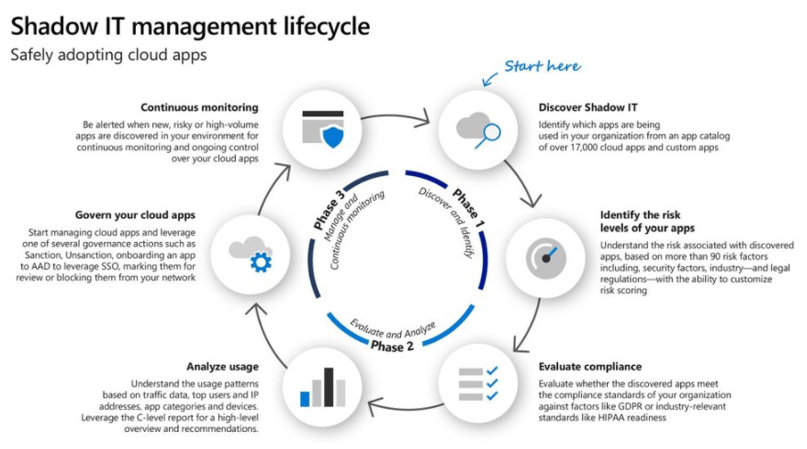
The Shadow IT Management lifecycle contains following main pillars:
Phase 1 – Discovery & Identify
- Discover Shadow IT
- Identify the risk levels of your apps
Phase 2 – Evaluate & Analyze
- Evaluate compliance
- Analyze usage
Phase 3 – Manage & Continuous Monitoring
- Govern your cloud apps
- Continuous monitoring
Govern & Monitor Cloud Apps – What options do I have?
Phases 1 & 2 are not covered in this blog, the focus is on phase 3: Govern & Monitor Cloud Apps’. Detailed information from different phases is found: Discover and manage Shadow IT tutorial | Microsoft Docs
When data has been ingested to MCAS where to start? I often receive this question and one way to start is by running ‘Cloud Discovery Executive’ report from Cloud App Security ‘Cloud Discovery’ dashboard to get overall understanding of SaaS application usage in your environment. The report highlights the key findings and recommendations for further actions.

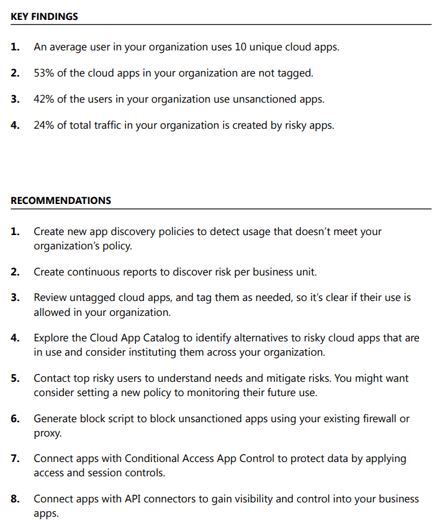
Control Apps
The recommendations provided by the report, you can start planning how to control applications on your environment. The flow chart below helps to decide what to do with discovered application.
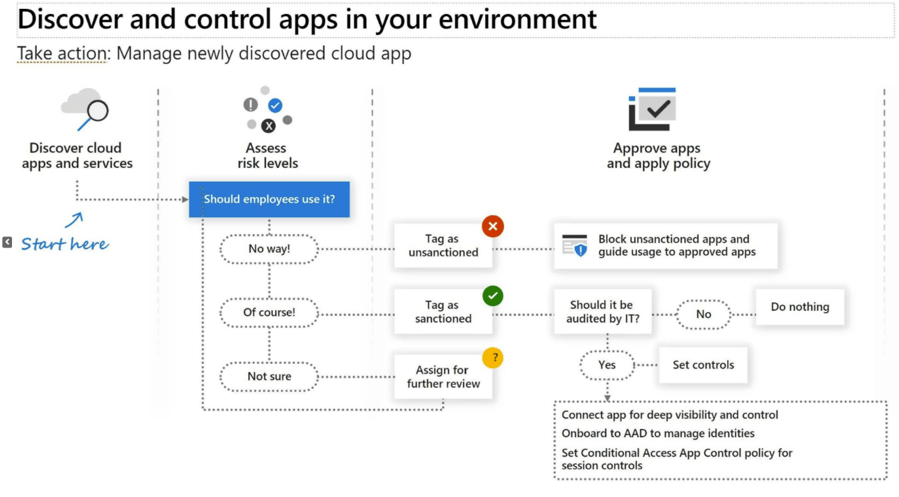
Further Review
If you are unsure what to do with the application assign it for further review and make decisions based on the detailed evaluation of the application.
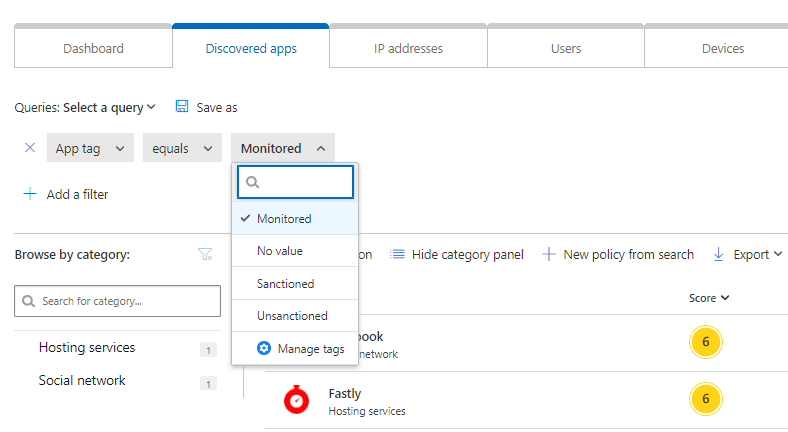
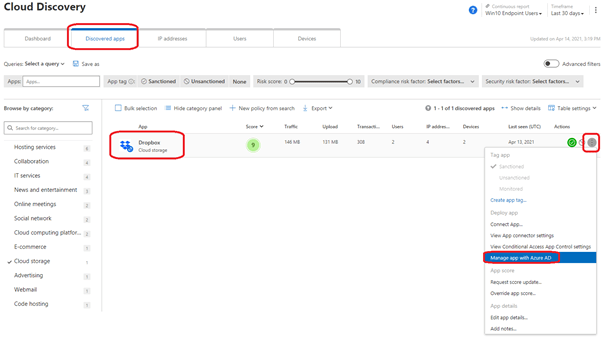
Sanctioned / Unsanctioned / Monitor applications
Decide whether an application is valid and allowed or prohibited to use in the organization. Admin can decide how to proceed with the application and assign “sanctioned”, “unsanctioned” or “Monitored“ tag to application (at the time of writing). The custom tags can be then used for specific monitoring purposes and filtering Cloud Discovery pages and creating policies.
If the application is not allowed to use in the organizations, it can be tagged as “unsanctioned”, and it can be blocked from the Windows 10 devices by the endpoint with integration between Microsoft Defender for Endpoint and Cloud App Security.
- This action will be propagated directly to Microsoft Defender for Endpoints, or any other integrated appliance like Zscaler, iBoss, Menlo or Corrata and can block access to the app.

When applications have tags “sanctioned, “unsanctioned” or “monitored” you can filter out the applications which doesn’t have tag. These are the apps that needs further review and decision after analysis phase.
Side note: Microsoft published “Warn and Educated Users on Risky App Usage” feature to public preview mode on 15th of August. With the feature you can apply soft block experience for end users when accessing monitored apps and users will have an option to bypass the block.

Manage discovered apps in Azure Active Directory
For apps that already appear in the Azure AD Gallery, you can deploy app to Azure AD and configure SSO for the app to leverage SSO capabilities. To do so, on the row where the relevant app appears, choose the three dots at the end of the row, and then choose ‘Manage App’ with Azure AD.
Set Controls for Application
If an application is valid for productivity, security and compliance perspective but needs additional controls it can be connected to Cloud App Security and assign Conditional Access app controls together with session controls.
- When available, use the app connector to enable advanced threat protection and DLP capabilities.
Protect apps via Conditional Access App Control
Microsoft Cloud App Security integrates with any identity provider (IdP) and helps to protect from data leaks, and data theft, in real-time with access and session controls. If Azure Active Directory (Azure AD) is used as IdP, these controls are integrated and streamlined for a simpler and more tailored deployment built on Azure AD’s Conditional Access tool.
Conditional Access App Control enables user app access and sessions to be monitored and controlled in real time based on access and session policies. With the access and session policies following scenarios can be achieved:
- Prevent data exfiltration
- Protect on download
- Prevent upload of unlabeled files
- Block potential malware
- Monitor user sessions for compliance
- Block access
- Block custom activities
Onboard Application for App Control
You can deploy any web app using any interactive single sign-on, using the SAML 2.0 authentication protocol or, if you are using Azure AD, the Open ID Connect authentication protocol to MCAS. When onboarding session controls for an application there are three (3) type of applications for onboard:
- Featured applications
- Full list of the supported apps is found from here
- Session controls works out of the box when pre-requisites are fulfilled
- Any Web App which is not in the list of feature app (but is recognized by MCAS)
- Not recognized apps
Onboard Featured Application
When pre-requisites are satisfied and app is integrated with Azure AD (or with other IdP solutions) proceed with the following order:
- Deploy Azure AD Conditional Access policy for the app
- Assign policy for the needed users/groups & target it only to app you want to onboard for session control
- Under Access Controls – Sessions – select Use Conditional Access App Control and choose a built-in policy (Monitor only or Block downloads) or Use custom policy to set an advanced policy in Cloud App Security, and then click Select.
- In my example I’m using custom policy to set an advanced policy in Cloud App Security
- Sign-in to app – verify that session is going through MCAS proxy. Otherwise the application is not seen on MCAS application list
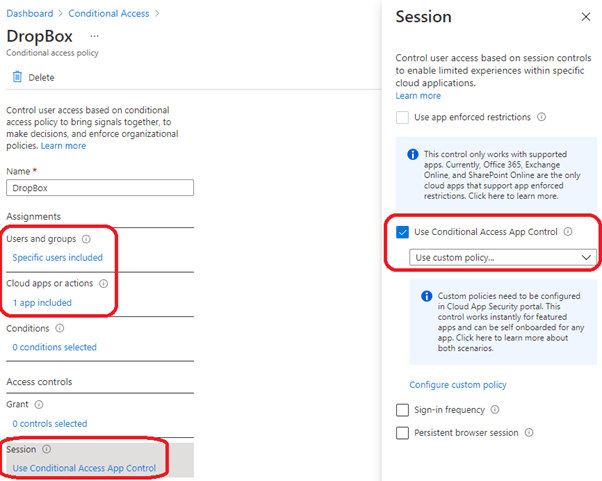
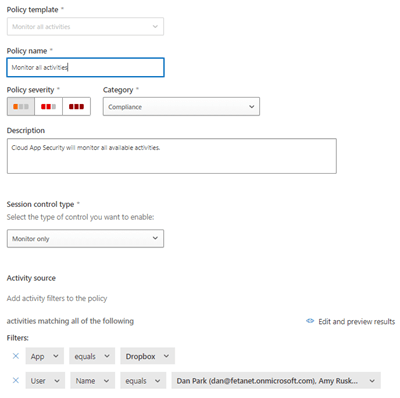
In Cloud App Security the policy is targeted to specific users who are using Dropbox Business
Any Web App
Featured applications which have the text “session control” underneath available controls are ready to onboard for session control.
Featured applications which have text “request session control” underneath available controls have two alternative approaches:
- Select “Request session control” to send request to MCAS Product Group for adding the app for session control
- Do it yourself from the right side of the page (3x dots) and edit app configuration


Custom Applications (not recognized)
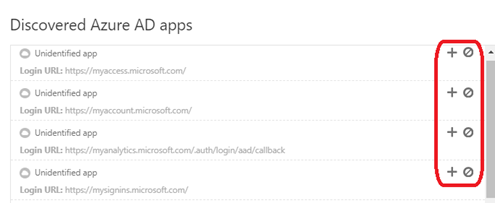
Session controls in Microsoft Cloud App Security can be configured to work with any web apps as mentioned before. If application is not found from the Cloud App Security app catalog, it will appear in the dialog under unidentified apps along with the login URL. When you click the + sign for these apps, you can onboard the application as a custom app.
Select ‘view apps’ from Conditional Access App Control apps main page

In discovered Azure AD apps page, you can either remove or add the app to MCAS app control.
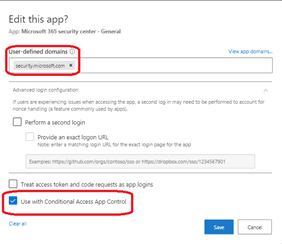
In the example below, I have added Microsoft Defender 365 portal (security.microsoft.com) as a custom application, as it is currently not automatically recognized. The app is also onboarded to the Conditional Access App control for session controls.
Azure AD – Authentication Context
The latest addition to app control mechanisms is Azure AD Conditional Access – Authentication Context which is integrated with the Cloud App Security (step-up authentication). With the ‘Authentication Context’ administrators can provide an extra layer of security inside of applications when needed.
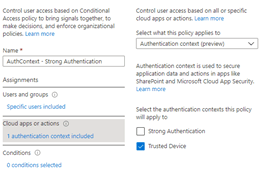
When Session control type is set one of the following types, you can require step-up authentication in MCAS session policies:
- Block activities
- Control file download (with inspection)
- Control file upload (with inspection)
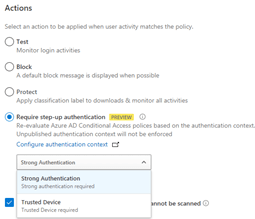
When this action is selected, Cloud App Security will redirect the session to Azure AD Conditional Access for policy re-evaluation, whenever the selected activity occurs. Based on the configured authentication context in Azure AD, claims request (challenge) such as multi-factor authentication and device compliance can be checked during a session.
More information from the links below:
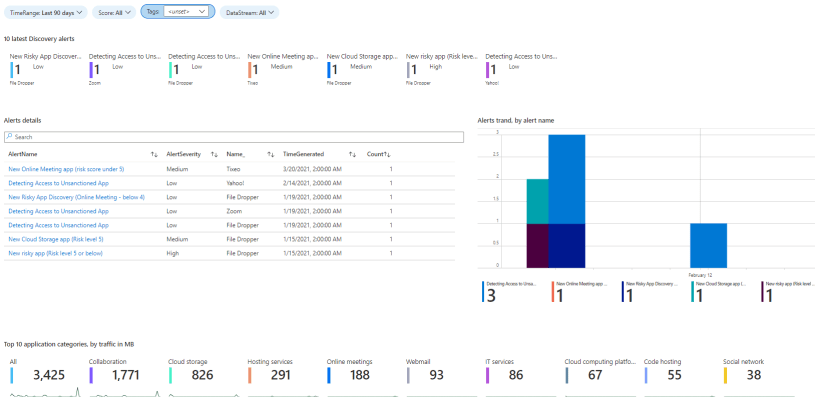
Continuous Monitoring
The last section of ‘Shadow IT’ management lifecycle is continuous monitoring. Environments are changing constantly, and end-users starts using new applications that might be risky for your organization. For that reason, it is important to actively monitor the environment to detect possible risky apps, threats, and data leaks to unwanted apps.
Cloud App Security ‘cloud discovery’ policies can help here. There are two kind of Cloud Discovery policies in MCAS:
- App Discovery policies
- App Discovery policy basically creates an alert when a new application is detected in the network.
- Additional parameters can be used to create the alert such as traffic in MB’s, the number of users, the application risk score, among others.
- Discovery Anomaly detection policies
- Anomaly detection is enabled in out of the box rules.
- If fine-tuning is needed it can be done by customizing the built-in policy or creating a new custom policy.
At the time of writing, there are total of 17 policy templates available for use in cloud discovery category in MCAS.
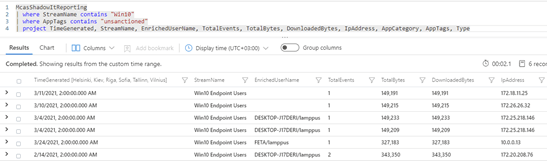
Azure Sentinel Workbook
With native Azure Sentinel ‘Cloud App Security’ data connector you can ingest alerts and cloud discovery data to Azure Log Analytics. When data has been ingested you can leverage built-in ‘Microsoft Cloud App Security’ workbook in Azure Sentinel for visualizing and analyze the application usage even further.
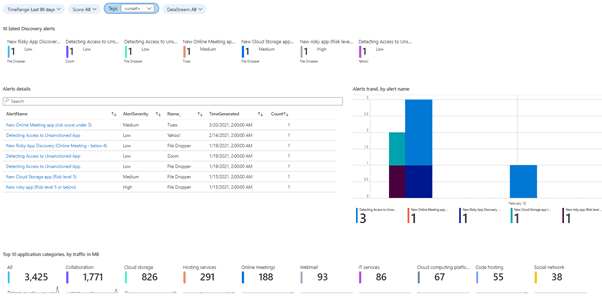
Use the filters (on top of workbook) to drill down to apps details. Example below contains unsanctioned app from two different reports, Win10 Endpoint users & ‘Cloud App Security Proxy’.


Summary
The topic in this blog is huge and it has been a long journey which I started in March 2021. Scenarios have been tested in my own lab environment and also in a couple of production environment to get as much data as possible. Technical deep-diver about the topic is ‘in progress’ so stay tuned.
In this blog I have covered how you can take control of the Shadow IT management lifecycle focusing on application governance. Hopefully, you find this blog useful in the journey of protecting your environment with Cloud App Security.
Nice thanks!
Great that you find it useful!