Microsoft security solution detection story continues. This time with Office 365 Advanced Threat Protection (O365 ATP). I haven’t touched much to O365 collaboration workload protection in my earlier posts. But now, this post is about O365 ATP alerts, and especially O365 ATP Safe Link alerts, in Microsoft Cloud App Security and Threat Protection suite.
Update 07/16/2020
After the recent Microsoft Cloud App Security release, the activity filtering doesn’t work as expected at the time of writing blog in May 2020. For this reason, I updated this blog to contain a workaround until the issue is fixed. The workaround can be found from the “Example – Safe Links policy (Updated version)” chapter.
What’s O365 Advanced Threat Protection (O365 ATP)?
In a nutshell, Office 365 Advanced Threat Protection (ATP) safeguards your organization against malicious threats posed by email messages, links (URLs) and collaboration tools.
It has Plan 1 and Plan 2 versions in terms of licenses, more information from here.
O365 ATP Policies
Following categories are available when configuring policies for O365 ATP. Descriptions from docs.microsoft.com.
ATP Safe Attachments
Provides zero-day protection to safeguard messaging system, by checking email attachments for malicious content. It routes all messages and attachments that do not have a virus/malware signature to a special environment, and then uses machine learning and analysis techniques to detect malicious intent. If no suspicious activity is found, the message is forwarded to the mailbox.
ATP Safe Links
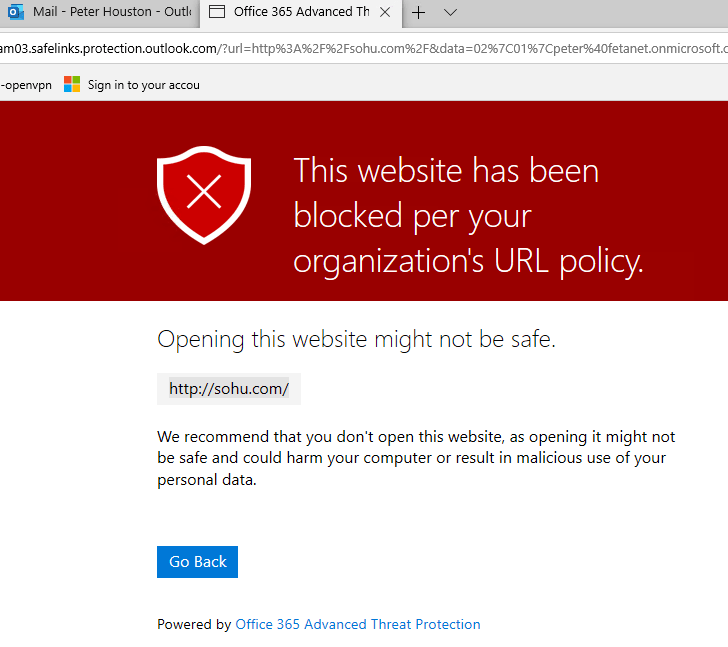
Provides time-of-click verification of URLs, for example, in emails messages and Office files. Protection is ongoing and applies across your messaging and Office environment. Links are scanned for each click: safe links remain accessible and malicious links are dynamically blocked.
ATP for SPO, ODfB and Teams
Protects organization when users collaborate and share files, by identifying and blocking malicious files in team sites and document libraries.
ATP anti-phishing protection
Detects attempts to impersonate your users and internal or custom domains. It applies machine learning models and advanced impersonation-detection algorithms to avert phishing attacks.
Gimme Alerts!!
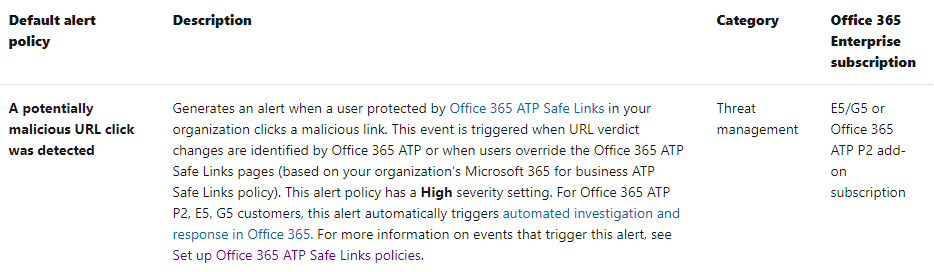
When O365 ATP is activated from M365 Security & Compliance Center the default set of alert policies is activated (descriptions found from here). Here is an example of an alert based on a safe attachment policy.

This default policy should do a trick but in my environment, I didn’t receive any alerts based on the default policy.
But, I can see activities and detections based on Safe Links policy in the new report template that was rolled out in March 2020.
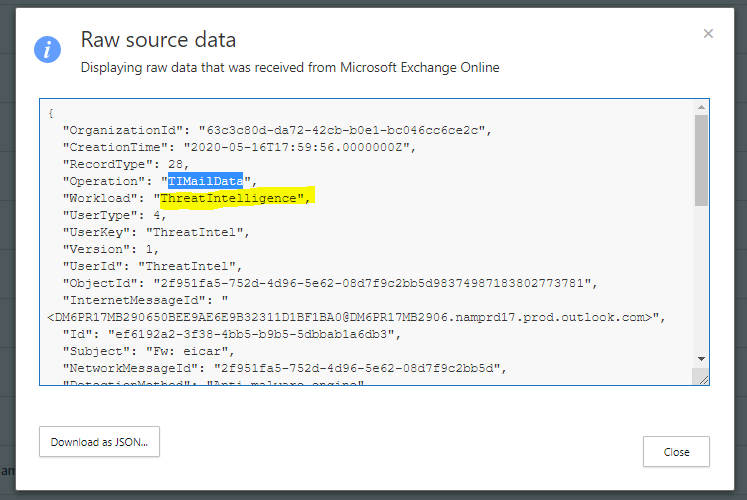
O365 Management Activity API
O365 ATP events are found from O365 Management Activity API. If you would like to send events and alerts to 3rd party SIEM you should create audit.general subscription to pull the O365 ATP events to the SIEM.
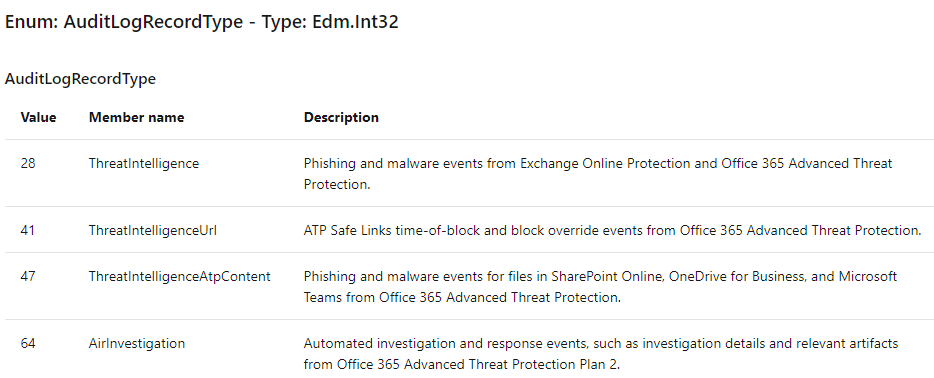
Following values of AuditLogRecordTyp are relevant fo O365 ATP events:
Cloud App Security
In case there is a need for alert customization (or you want to centralize alert policy management), you can find O365 ATP detections in the Cloud App Security activity log. This means that you can create custom policies based on the activity log data.
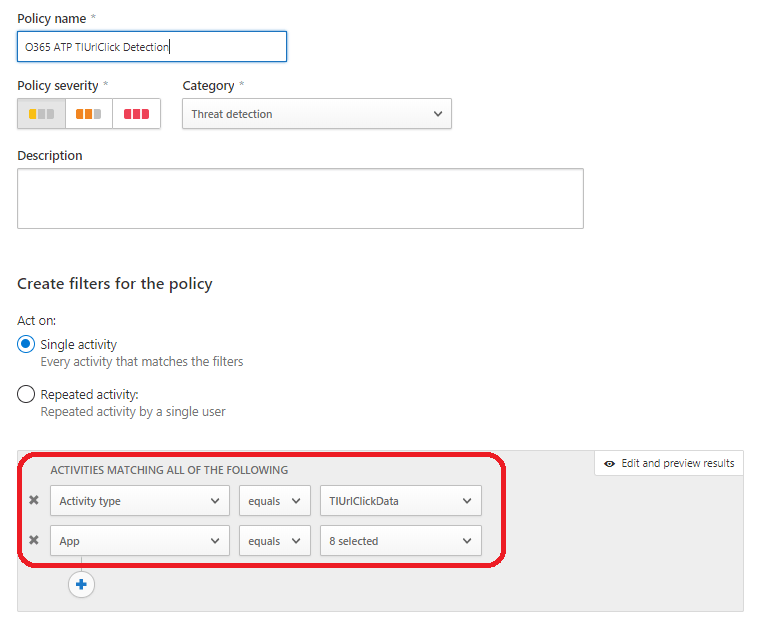
Example – Safe Links policy (Updated version)
As said, there seems to be an issue in the MCAS platform that prevents using some of the activities as a filter (most probably it’s going to be fixed quite soon but the schedule is unknown).
In meanwhile when waiting for it to be fixed, there still is a workaround available. You can use the following command/URL to achieve the same result than before (replace fetanet with own domain name):
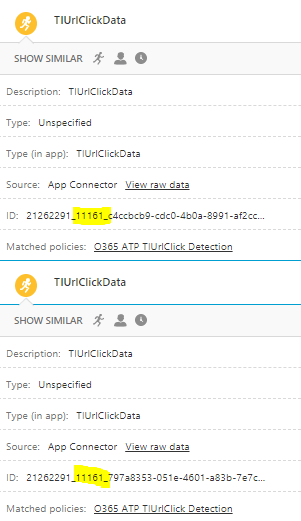
Every TIUrlClickData has an activity ID “11161” that can be used as a filter when making searches in the Activity Log or creating new policy.
When the issue in the platform has been fixed earlier method presented in the next chapter should work as expected.
Example – Safe Links policy
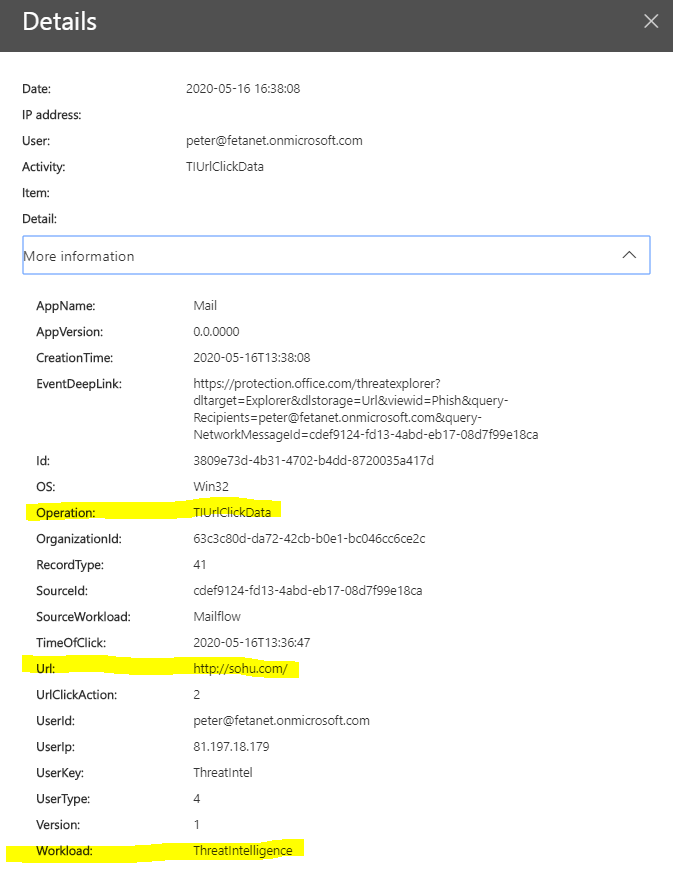
You need to create a custom policy that detects “TIUrlClickData” from ThreatIntel provider which does the magic in here. The reason I did this one is that Security & Compliance Center default policies didn’t work as expected.
When MCAS receives the audit logs from O365 API you can see something like this in the alert page and the activity logs
The same event data is found from the O365 Unified Audit Log (UAL) and as mentioned above, from the O365 Management Activity API audit.general category. But, for some reason nothing in O365 Security & Compliance center alerts.
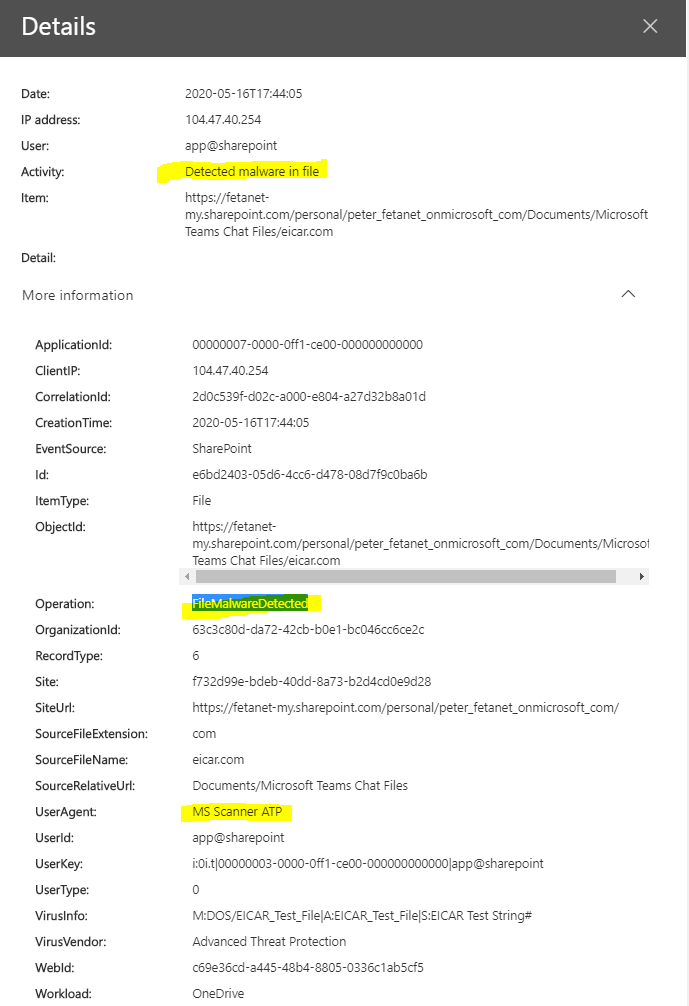
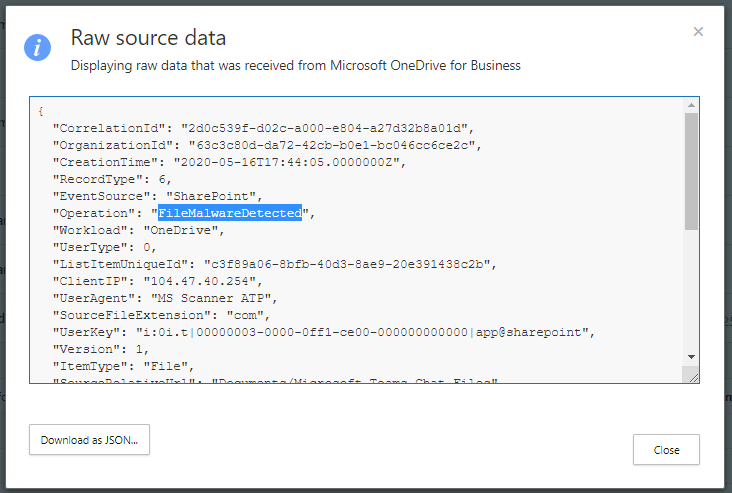
Just to highlight that there are events about malware detection. Alert about this activity is created by default policy as expected and MCAS activity log has events based on this activity available.
Microsoft Threat Protection suite
The new Microsoft Threat Protection suite in M365 Security Center is a brilliant tool for incident management in M365 workloads. In my example case, the activity event is first identified in ThreatIntel workload (O365 ATP engine) and actual alert is raised in Cloud App Security. For that reason, the alert is found from MTP where it can be managed.
If alert is raised in O365 based on default policies it’s found from MTP.
What has been surprising, in a positive way, to see is that when incident/alert status is changed in the source the status is synced immediately back to MTP, awesome work from Microsoft!!
Happy monitoring, until next time!










Hi
I cant see the the TIUrlClickData activity when creating a policy, do i need to setup something to see this?
Hi,
When you have created the policy you should see alert created by the policy when activity is detected. To verify, first check from UAL (Unified Audit Log) that the activity exists in there. If it does, confirm same from mcas activity log.
And of course, I assume that you have O365 ATP safe links policy in place?
I can trigger the TIUrlClickData in my tenant and it is visible in both the UAL and MCAS Activity logs, however the “type” in the MCAS Activity Log is “unspecified”, therefore you cannot create a policy based on it as the “TUUrlClickData” isnt listed as an activity type when crafting a policy.
I am not sure how you were able to achieve this in your tenant?
Hi,
If you check pics from my blog you can see that the activity type is ’TIUrlClickData’. Unfortunately, I’m not able to attach pics for this conversation.
Anyway, I can test later on this week do I still get TIUrlClickData activity to mcas or has ms changed something in the backend
That’s what’s so confusing as I dont have that option – if you could retest now that would be appreciated as I suspect something has changed in a recent release?
Yes, definitely! I have two tenants where I can test behavior. Will get back to you later on this week. Do you want me to send email to you or reply in here?
email is fine – thanks Sami!
Hi Sami,
I got the same problem with the default alert “A potentially malicious URL click was detected” that it is not triggered with the user protected by AIP Safe link. We only have M365 Business standard and ATP P2 license so is it possible to make a custom alert with activiy:TIUrlClickData ?
Hi,
I have to admit that I’m not a licensing expert:) I haven’t test with the combination you have in place. Do you have MCAS in place? MCAS has different versions available, see this one
https://docs.microsoft.com/en-us/cloud-app-security/editions-cloud-app-security-o365
Possible O365 version would do a trick when we are talking about O365 Apps only.
Hi Sami,
Thanks for your quick reply. Unfortunately we don’t have MCAS in place. We are opening a ticket for the alert problem, but still do not find out where is the issue.
Do you have any information about this alert problem from MS?
Unfortunately no, I haven’t figure it out.
If possible, could you please share ms response. I would like to know why the default alert doesn’t work.
One thing you could try is to create custom alert in O365 side with same parameters than the default alert rule has.
By doing so you can verify does the mechanism work at all in O365 side and does it receive correct audit data.
I’m booking a remote session with the engineer to check in more details.
About the custom alert, they do not have the parameter/activity for the clicking malicious URL.
I will share with you the information if we find out what’s the problem.
Hi Sam, I am following your process and I am able to see the component of TIUrlClickData in MCAS, but I dont have hits in my policy. Do you know what might be causing the issue? I already put on the default global policy of Safe Links, the URL to be blocked. Thoughts?
Hi Emmanuel,
If you search the activity from the MCAS activity logs are you able to find “TIUrlClickData” from there?
Lately, I have seen huge delays in data processing in my own MCAS instances, and if you are experiencing the same that might explain some of the issues.
Thanks,
Sami
Thanks my friend Sami, you were totally right the alert appeared but it was a little delayed like 6-8 hours to appear. Now I see the alert.
Great to hear! In my case it also took a while😊