A long waited feature has seen a daylight, Azure Storage Account data connector in Azure Sentinel. Official Microsoft documentation – What’s new in Azure Sentinel | Microsoft Docs.
In the last couple of years there has been lot of development activities around resources diagnostics settings configuration and Azure Policy engine. Currently, Azure Policy ‘allows you to apply a common set of diagnostics logs settings to all (current and future) resources of a particular type whose logs you want to ingest into Azure Sentinel’.
Azure Key Vault and Azure Kubernetes were announced earlier and are now in GA, together with Azure SQL Databases connector. So in a nutshell:
- Azure Storage Account – in preview
- Azure Key Vault – GA
- Azure Kubernetes – GA
- Azure SQL for Databases – GA
What’s new in Azure Sentinel | Microsoft Docs,
Connect Azure Storage account diagnostics logs to Azure Sentinel | Microsoft Docs
Background
I have been working with cloud security monitoring intensely last two (2) years and I have seen that many organizations are lacking behind on Azure resources security monitoring. This means that audit plane activities are not fully audited.
@JoosuaSantasalo wrote excellent blog about resource manager management and data plane differences a while a ago. Read full blog from here.

Configuration
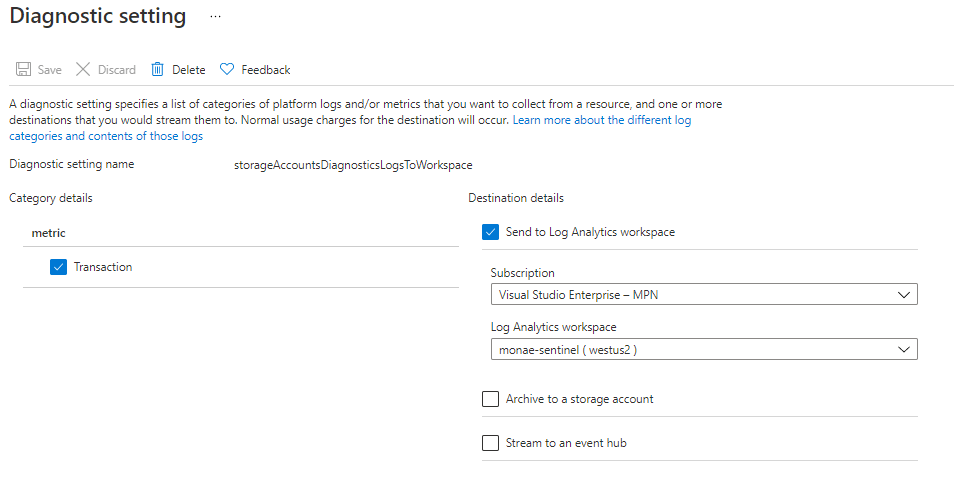
What’s needed to establish the scenario and storage account audit data to Azure Sentinel? Basically, configuration of diagnostics settings to needed resources and some KQL magic, that’s about it.
Azure Policy
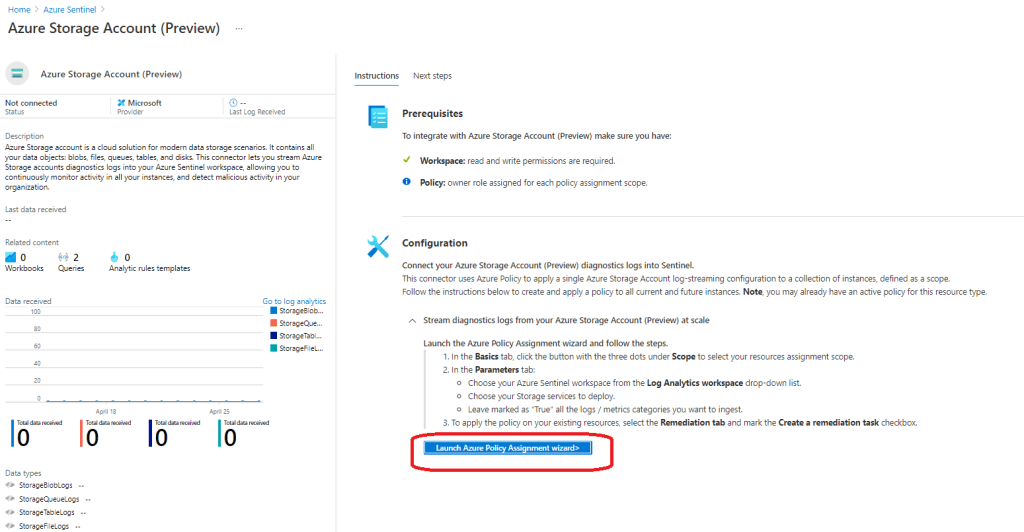
An easiest way to establish the scenario is to configure Azure Policy that sets the diagnostics settings to the resources.
- Navigate to Azure Sentinel and ‘Azure Storage Account’ data connector – select ‘launch Azure Policy assignment’, or do it directly from the policy management console
- Select scope for you Azure Policy definition (I used Azure subscription level in my demo environment)
- Define settings and storage services based on your needs
- By default, the policy affects only to newly created resources. If you will create remediation task, like I did, all existing resources will be impacted
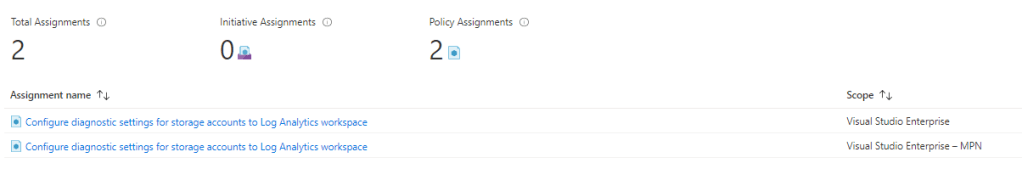
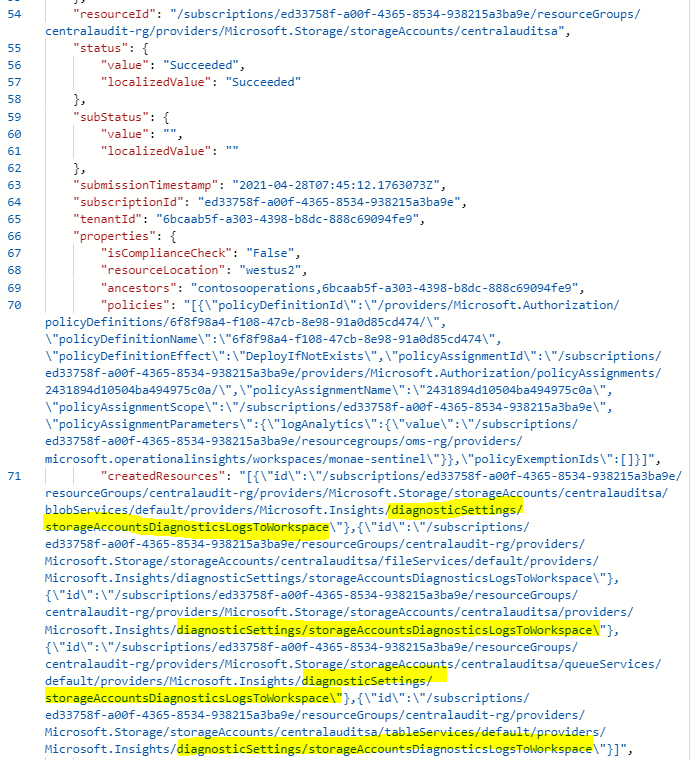
When Azure Policy is configured it’s seen on the assignments blade and implementation can be verified from the Activity Logs.
When policy has been implemented the resources are either compliant or non-compliant.
Side note: it took at least 12 hours to “resources by compliance state” graph to update event though the resources reported successful remediation. If you want to trigger scan manually and don’t want to wait the policy schedule it can be triggered manually – Get policy compliance data – Azure Policy | Microsoft Docs
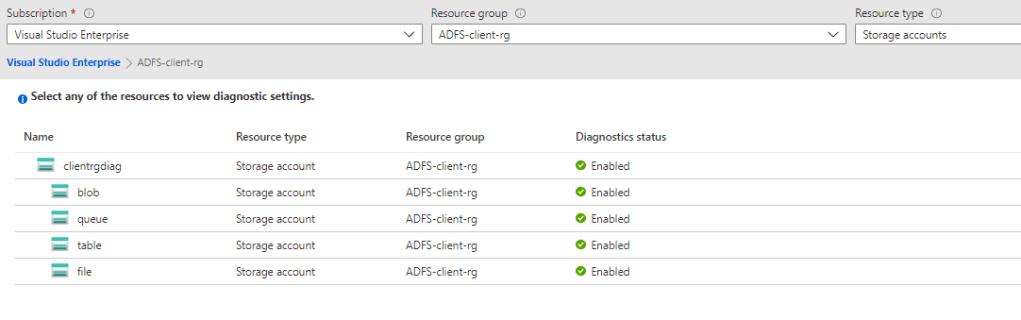
For the resources itself, it’s seen that configuration has been implemented
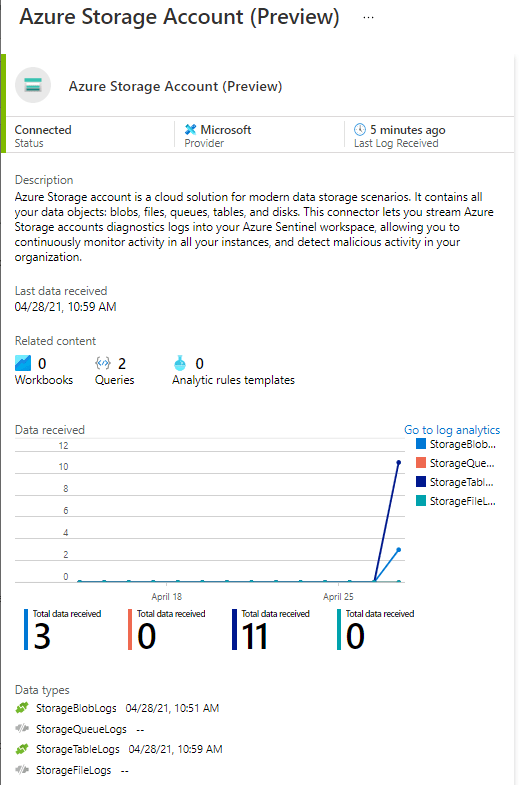
From the Azure Storage Account data connector we can now see the ingested data.
Built-in KQL Queries
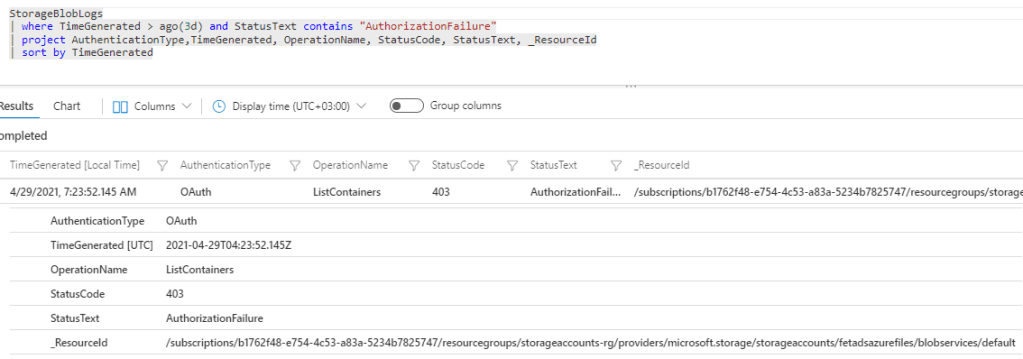
List storage accounts from last thee days period.
StorageBlobLogs
| where TimeGenerated > ago(3d)
| project TimeGenerated, OperationName, StatusCode, StatusText, _ResourceId
| sort by TimeGeneratedList top 200 storage accounts from last 7 days.
StorageBlobLogs
|where TimeGenerated > ago(7d)
| top 200 by TimeGenerated desc
| sort by TimeGeneratedIf someone is trying to access to storage account
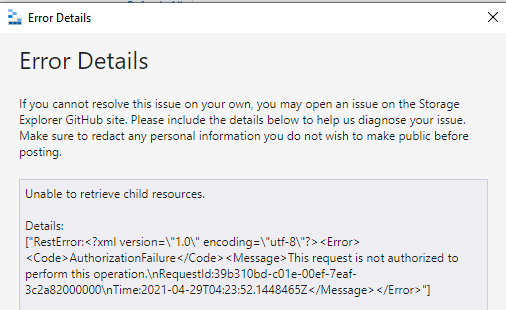
It can be seen on Log Analytics
Until next time!